Table of Contents
- 10+ Audit Log Templates in PDF | WORD
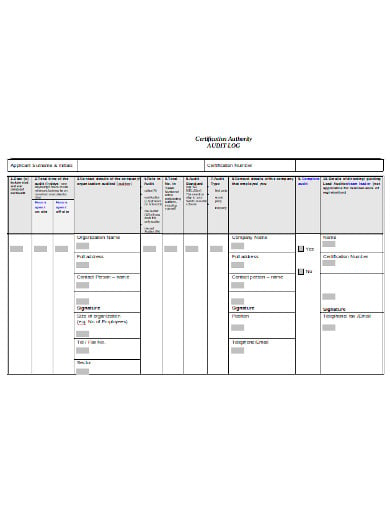
- 1. Audit Log Template
- 2. Audit Log Review
- 3. Hitachi Audit Log
- 4. Audit Log Tamper Detection
- 5. Privacy Audit Log
- 6. Audit Log Offline
- 7. Audit Log Documentation
- 8. Audit Log in DOC
- 9. Audit Log Example
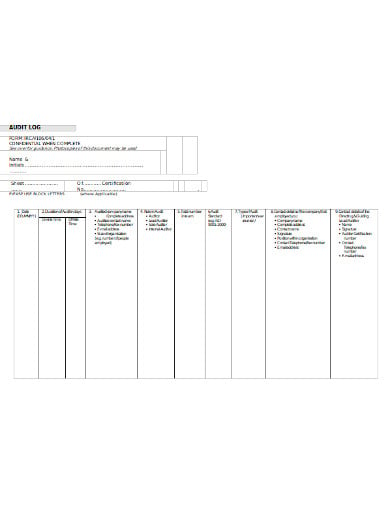
- 10. Directorate Audit Log
- 11. Audit Log Format
- 5 Best Practices for Audit Logging
- What are the Uses of an Audit Log?
- What is Audit Trail?
- Benefits of Having a Detailed Audit Log
- How Long Can You Maintain an Audit Log?
10+ Audit Log Templates in PDF | WORD
A particular document that records the information about resources including the destination addresses, source addresses, user login information, and timestamps is known as the audit log. Auditors usually require proof of the controls, control monitoring, and event information. It refers to the record of sequential activities that are maintained by the application or system.

10+ Audit Log Templates in PDF | WORD
1. Audit Log Template
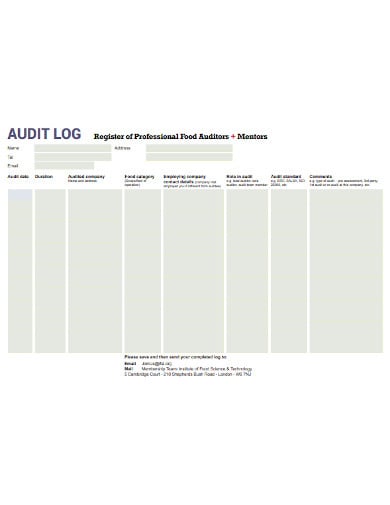 ifst.org
ifst.org2. Audit Log Review
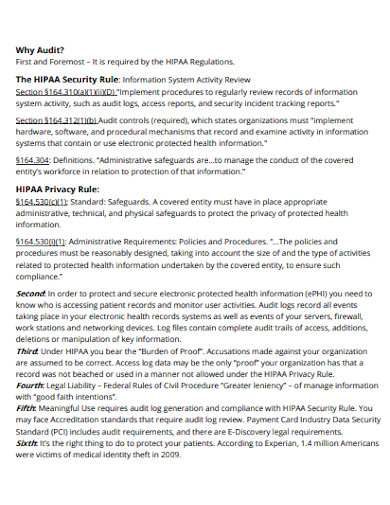 cdn.hubspot.net
cdn.hubspot.net3. Hitachi Audit Log
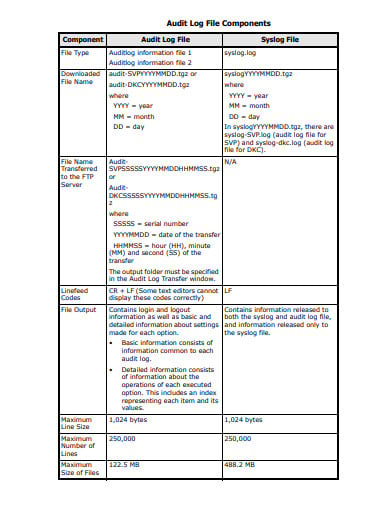 support.hitachivantara.com
support.hitachivantara.com4. Audit Log Tamper Detection
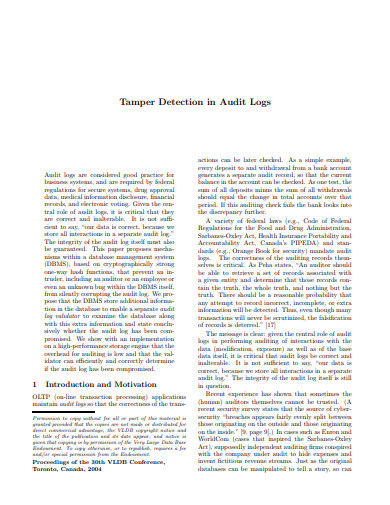 vldb.org
vldb.org5. Privacy Audit Log
 semanticweb.org
semanticweb.org6. Audit Log Offline
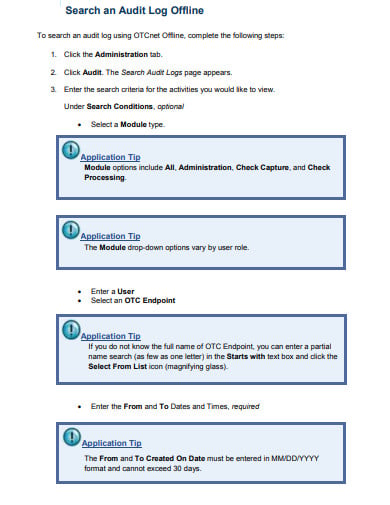 fiscal.treasury.gov
fiscal.treasury.gov7. Audit Log Documentation
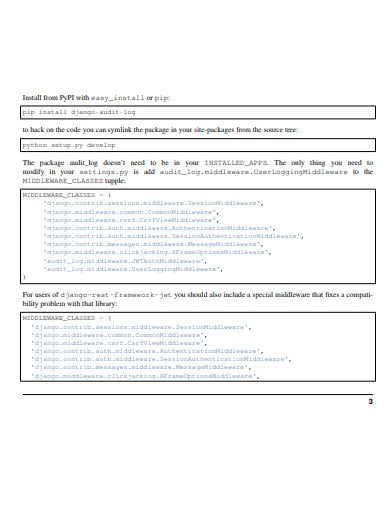 buildmedia.readthedocs.org
buildmedia.readthedocs.org8. Audit Log in DOC
 saatca.co.za
saatca.co.za9. Audit Log Example
 hance.co.kr
hance.co.kr10. Directorate Audit Log
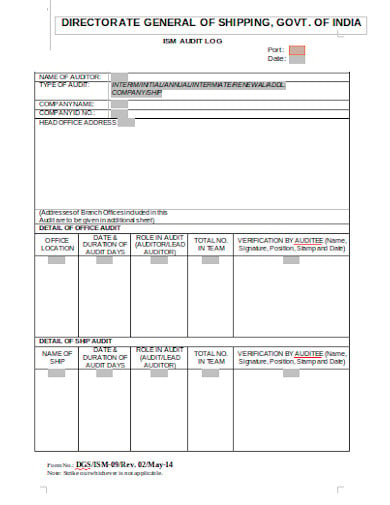 mmd.gov.in
mmd.gov.in11. Audit Log Format
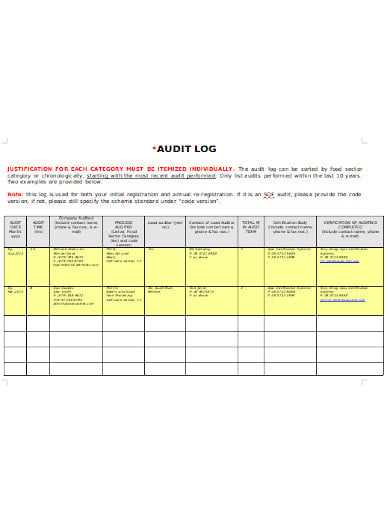 sqfi.com
sqfi.com5 Best Practices for Audit Logging
-
Protects the Logs
The logs usually contain some legally protected sensitive data and although they track your security positions, you still need to ensure that malicious actors cannot gain access to them. It is recommended that organizations create and maintain a secure log management structure. A fail-open option may appear beneficial as it continues to operate no matter what happens. This configuration is used by organizations when access matters more than authentication. Audit logging generally focuses on access control logging. Hence, you would want to use a fail-safe that protects other system components by including an external bypass switch device.
-
Ensures Unity
Giving importance to log management across the organization enables data unity from within. You can establish goals that are arranged with applicable laws and regulations. Then you can start creating internal policies that focus on retention and monitoring that will help in reducing the risk.
-
Look for Audit Logging Program
You can establish some policies and procedures for logging standards and some guidelines that will help you to more effectively assimilate log monitoring across the enterprise. Audit logs also provide you with two types of information. It allows you to track access to the system and also enables continuous monitoring for continuous compliance. To make your overall compliance process smooth, a dual-purpose audit logging program can help in reducing the time spent on monitoring while increasing security and compliance.
-
Supplies Resources to Direct Responsibilities
You must make sure that you not only hire the appropriate number of employees to review some access logs but also the tools that make this an efficient process. Some resources may include technical guidance, sharing some information with the staff, provide tools or tool documentation, and training staff.
What are the Uses of an Audit Log?
Audit logs are usually used for tracking activities that impact the environment, tracing the location of the activities to maintain data unity. Audit logs are also used for the following purposes:
-
Audits
An audit log gives the chronological record of an event. The auditor uses the audit log to check for abnormalities or noncompliance when he/she comes to review your compliance for certification purposes.
-
General Amendment and Business Progression
Audit logs also help in enabling the security team to reconstruct events after some problem occurs. This documentation provides the security administrator with the information that is required to recover rapidly from an intrusion.
-
Evidence
The audit log can also be used as a piece of evidence to show some appropriate event management.
-
Threat Detection
Analyzing the audit logs regularly helps in providing insight into any kind of abnormal behavior in case you want to connect them to real-time tracking systems.
What is Audit Trail?
Audit trail refers to the log records that helps in identifying a particular transaction or event or view or access them. It is also defined as a record that portrays who has accessed a computer system, when was it accessed, and what other operations were performed. It means the step-by-step record with the help of which accounting or trade data can be easily traced to its source. Audit trails are generally used to verify and track many types of transactions including accounting transactions and trades in some brokerage accounts. It is also used mostly when the accuracy of an item needs to be verified. This can be useful tools when determining the validity of accounting entry, source of funds, etc.
Benefits of Having a Detailed Audit Log
-
Increased Security
You can protect a business from liability during legal battles if you have a detailed audit log. These logs also help the companies monitor data for any security breaches or internal misuses of information. It also ensures that proper document protocols are followed properly, and to prevent or track down any kind of fraud.
-
Risk Management
Audit logs also play an important role in the overall risk management strategy of a business, gives a demonstration to the customers, business partners, and regulators that an organization has made a thorough effort to protect against and prevent any problems before they occur.
-
Demonstrate Compliance
Many organizations must comply with the tax regulations as well as federal laws, along with the industry-specific regulations. Audit logs can also be used as proof of regular compliance during an audit and can also help a company fulfill its record-keeping requirements for compliance purposes.
-
Detailed Awareness
An audit log can be used to gain insight into which investors or partners are most interested in business as an audit tracks how long and how frequently individual users access a document. This will enable the company to be more strategic with its negotiations. It offers both startups and established companies the insight or the awareness abilities that they need to increase efficiency and security in a reliable, provable way.
How Long Can You Maintain an Audit Log?
It might be difficult for many organizations to have long term maintenance of audit logs because the logs may occupy extensive storage space that may not be readily available. But, if possible, you can maintain the audit trail for the life o the records. These can become extremely useful in historical reporting and also in solving problems in the future.






