Table of Contents
- FREE 10+ Data Security Plan Templates in PDF | MS Word
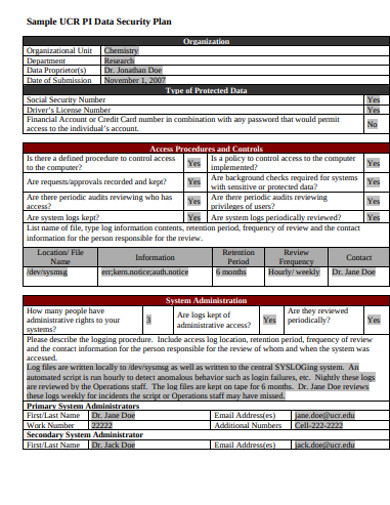
- 1. Sensitive Data Security Plan
- 2. Institute Data Security Plan Template
- 3. Sample Data Security Plan Template
- 4. Information Data Security Plan
- 5. Data Service Security Plan Template
- 6. Format Data Security Plan Template
- 7. Privacy and Data Security Plan Template
- 8. IT Data Security Plan Template
- 9. System Data Security Plan Template
- 10. Basic Data Security Plan Template
- 11. Technology Data Security Plan Template
- Elements of a Data Security Plan
- FAQ’s
- What is a data security plan?
- What are the essential elements of data security?
- How do you ensure data security?
- What is a written information security program?
- Why is data protection important?
FREE 10+ Data Security Plan Templates in PDF | MS Word
The Data Security Plan (DSP) narrates the survey strategies and data handling settlements that will be executed to secure study data and protect confidentiality. Attaining the objectives of data security is a never-ending process, which includes managerial, physical and technical solutions. On the basis of data security policy, a set of user rules and plans concerning data security will be drawn up for the preserved organization.

FREE 10+ Data Security Plan Templates in PDF | MS Word
1. Sensitive Data Security Plan
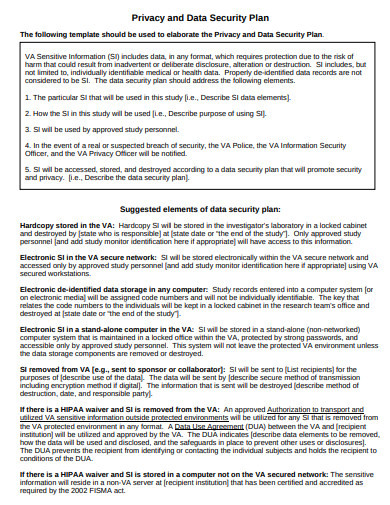 irb.ucsd.edu
irb.ucsd.edu2. Institute Data Security Plan Template
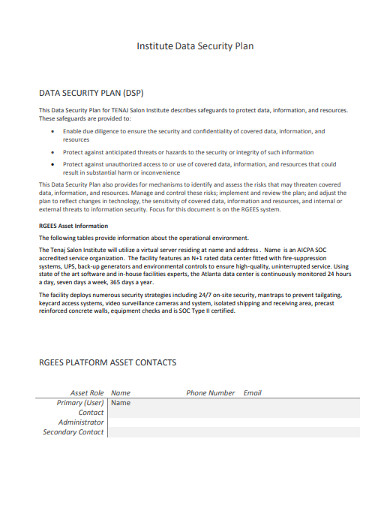 tenajsaloninstitute.edu
tenajsaloninstitute.edu3. Sample Data Security Plan Template
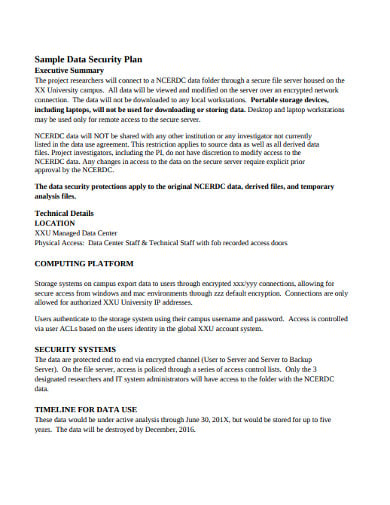 childandfamilypolicy.duke.edu
childandfamilypolicy.duke.edu4. Information Data Security Plan
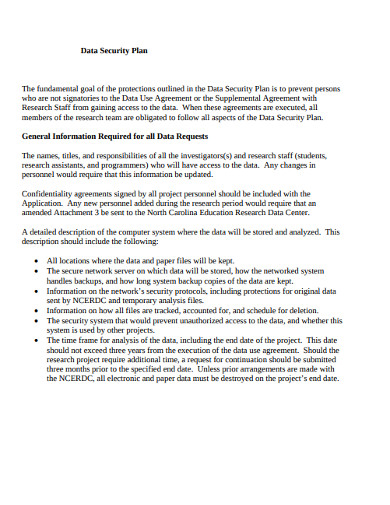 childandfamilypolicy.duke.edu
childandfamilypolicy.duke.edu5. Data Service Security Plan Template
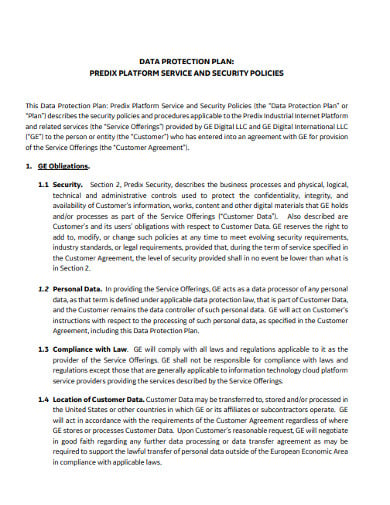 ge.com
ge.com6. Format Data Security Plan Template
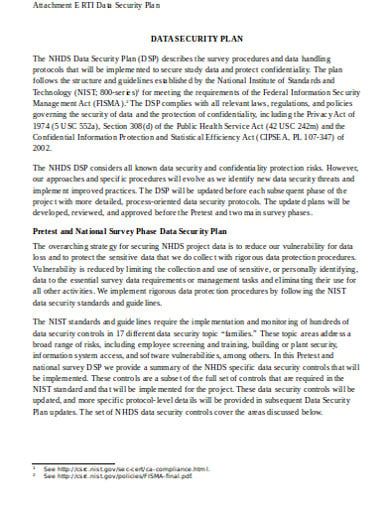 reginfo.gov
reginfo.gov7. Privacy and Data Security Plan Template
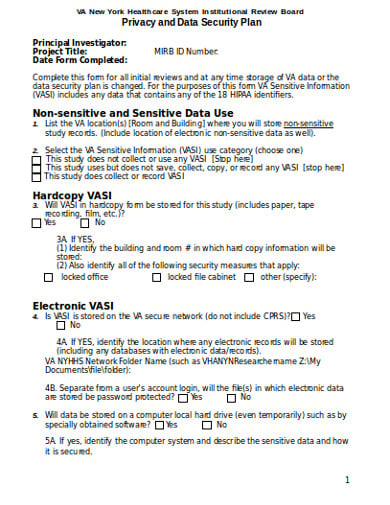 nyharbor.va.gov
nyharbor.va.gov8. IT Data Security Plan Template
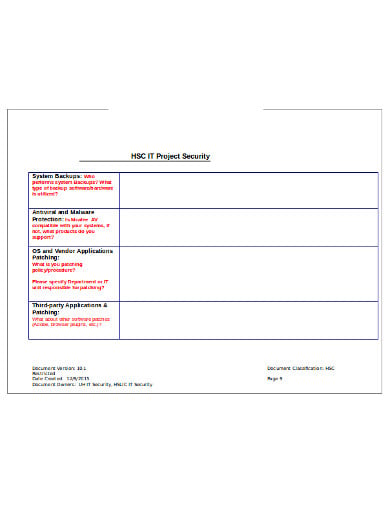 hsc.unm.edu
hsc.unm.edu9. System Data Security Plan Template
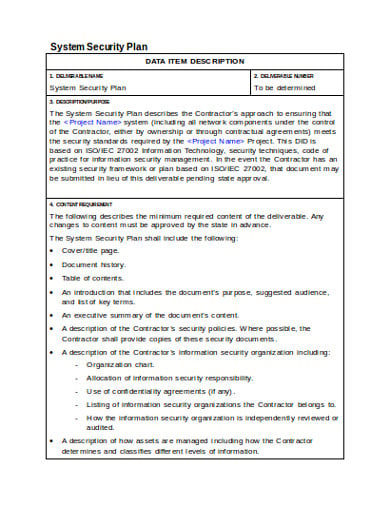 bestpractices.ca.gov
bestpractices.ca.gov10. Basic Data Security Plan Template
 cnc.ucr.edu
cnc.ucr.edu11. Technology Data Security Plan Template
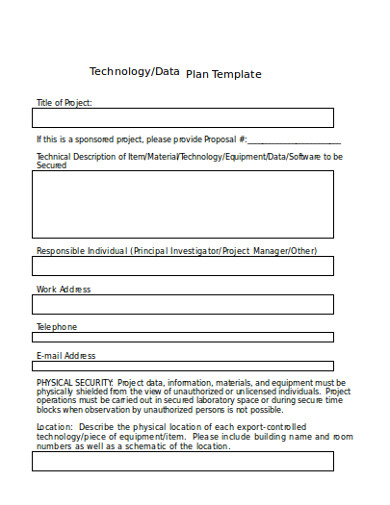 researchprotections.appstate.edu
researchprotections.appstate.eduElements of a Data Security Plan
Every worker must recognize his or her responsibility to protect company information. Workers do need consistent behavioral guidelines when it relates to their data-interaction. To do this, the data protection policy needs to be written, comprehensible and legally binding. This will detail the procedures that help to protect corporate data and confidential information for staff, clients, businesses and third parties.
Safeguard Data Privacy:
Workers must recognize that the privacy policy is a guarantee to their customers that their information will be secured. Data would only be used in ways that safeguard consumer identity and data confidentiality. Your staff and organizations must, of course, be following all relevant laws and regulations.
Establish Password Management:
For all workers or temporary staff who will have access to corporate resources, a password policy should be created. In general, the complexity of passwords will be calculated according to job functions and the specifications of data protection. None should share passwords.
Govern Internet Usage:
Many individuals use the internet to the harm that can result without a thought. Abuse of the Internet by employees may put your business in an uncomfortable, or even illegal, situation. The setting of limits on employee internet use in the workplace will help to prevent these situations. It is up to each company to determine how workers can and should access the internet. You want workers to be successful and that could be the key reason to restrict the usage of the Internet, but security issues can also determine how directives are implemented on the internet.
Manage Email Usage:
Most data violations stem from employee email abuse that can lead to data loss or theft and unintended installation of viruses or other malware. Specific standards about email usage, message content, encoding, and file retention should be developed.
Govern and Manage Company-Owned Mobile Devices:
As companies offer their workers with mobile devices to use, a structured process will be enforced to help ensure that mobile devices are safe and suitably used. The minimum criteria would be to allow workers to be responsible for protecting their devices from theft and to allow password protection in compliance with the password policy.
Develop a Worker-owned Mobile Devices Approval Process:
With the enhanced capacities of consumer devices, such as mobile phones and tablets, interconnecting these devices to company applications and infrastructure has become simple. Using these tools to interconnect with business email, calendar and other services may blur the boundaries between business controls and user controls. Employees who demand and are allowed to access business information through their devices should recognize and embrace the corporation’s restrictions and safeguards.
Govern Social Media:
All users of social media need to be mindful of the dangers related to social media communication. With any company seeking to use social networking to promote its activities and connect with its clients, a clear social media strategy is important. Good governance will help ensure that workers talk within their corporation’s boundaries, and follow best practices in data privacy.
Oversee Software Copyright and Licensing:
There are also valid reasons for workers to honor the copyright and licensing arrangements with software. Companies are expected to conform to the terms of the software licensing contracts and any access limits will be made available to employees. Employees can also not download and use software which the organization has not tested and approved.
Report Security Incidents:
A mechanism must be in place to disclose malicious software to workers or contractors if it is unintentionally imported. All staff must know how to address malware attacks, and what measures to follow to minimize harm.
FAQ’s
What is a data security plan?
Professional tax filers are informed that federal legislation mandates them to develop a formal plan for protection of information to protect the data of their clients. Creating and executing a written data protection plan is essential to protecting their customers and their company.
What are the essential elements of data security?
To secure data, the analysis and enhancement require a solid, robust application security framework. A proper data security plan includes six essential elements. These elements include availability, utility, integrity, authenticity, confidentiality, and non-repudiation. If any of these six components is missing, the security of information is inadequate, and data safety is at threat.
How do you ensure data security?
For any business owner data protection should be an important area of concern. When you recognize all the important information that you store virtually — from financial records to private information about clients — it’s not difficult to see why one violation could severely harm your business.
What is a written information security program?
A WISP, also known as Written Information Security Program, is the file with which an agency sets out the financial, technological and physical protections by which it preserves the privacy of the personally identifiable information it holds.
Why is data protection important?
Data security is the mechanism by which sensitive information is shielded from theft, misuse or failure. Data security is becoming more relevant as the volume of data generated and processed continues to increase at exponential levels. There is also limited tolerance for interruption which may make access to sensitive data difficult.






