Table of Contents
- FREE 11+ Security Incident Response Plan Templates in PDF | MS Word
- 1. Computer Security Incident Response Plan Template
- 2. Basic Security Incident Response Plan
- 3. Data Security Incident Response Plan Template
- 4. Information Security Incident Response Plan Sample
- 5. Security Incident Response Plan Template
- 6. Security Incident Response Plan Example
- 7. Security Incident Response Plan in PDF
- 8. Credit Card Security Incident Response Plan Template
- 9. Standard Housing Data Security Incident Response Plan
- 10. Basic Security Incident Response Plan Template
- 11. IT Security Incident Response Plan Form
- 12. Data Security Incident Response Plan Format
- Importance of An Incident Response Plan
- Roles in a Security Incident Response Team
- FAQ’s
- What is a security incident response plan?
- What are the five steps of incident response in order?
- What constitutes a security incident?
- What is the first step in security incident management?
- What is incident recovery?
FREE 11+ Security Incident Response Plan Templates in PDF | MS Word
Incident response refers to a coordinated approach to handling and managing the consequences of a security breach or cyber-attack, also known as an accident involving IT, computer accident or defense. The goal is to manage the issue in a way that limits harm and reduces the time and cost of recovery. An incident response strategy is a series of guidelines to help IT workers track, react, and recover from incidents related to network security. Such kinds of plans tackle problems such as cyber-crime, data loss, and regular work-threatening service outages.

FREE 11+ Security Incident Response Plan Templates in PDF | MS Word
1. Computer Security Incident Response Plan Template
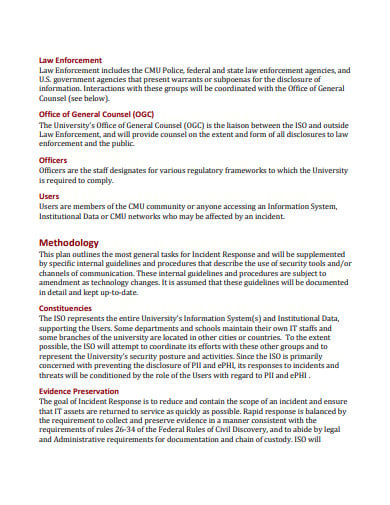 cmu.edu
cmu.edu2. Basic Security Incident Response Plan
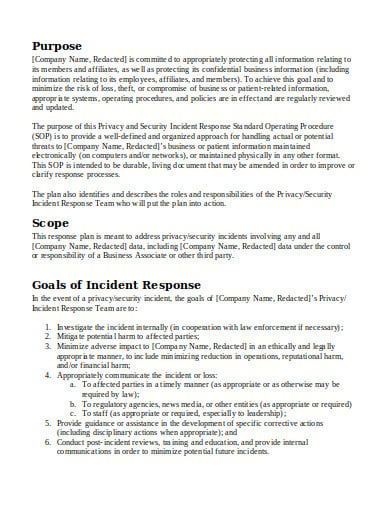 corporatecompliance.org
corporatecompliance.org3. Data Security Incident Response Plan Template
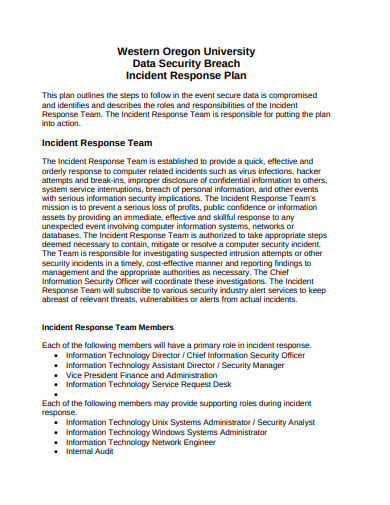 wou.edu
wou.edu4. Information Security Incident Response Plan Sample
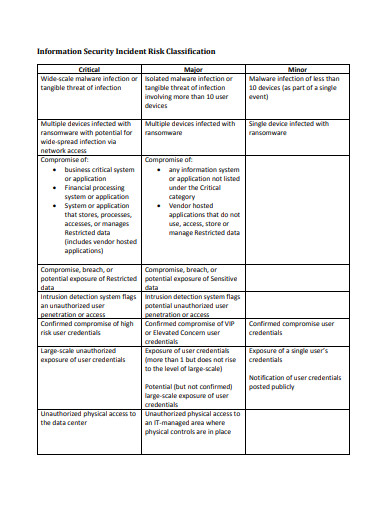 unh.edu
unh.edu5. Security Incident Response Plan Template
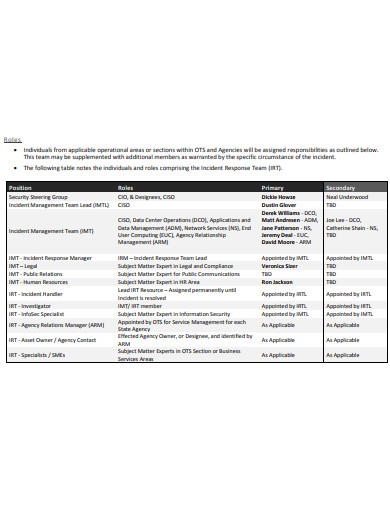 doa.la.gov
doa.la.gov6. Security Incident Response Plan Example
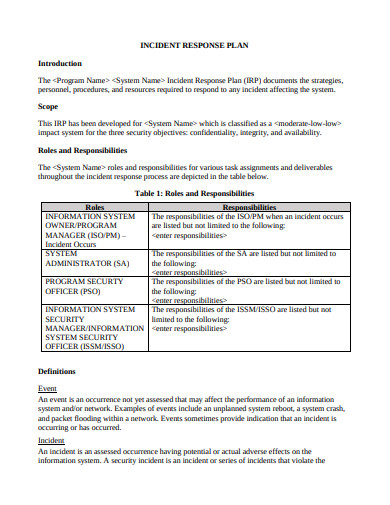 dss.mil
dss.mil7. Security Incident Response Plan in PDF
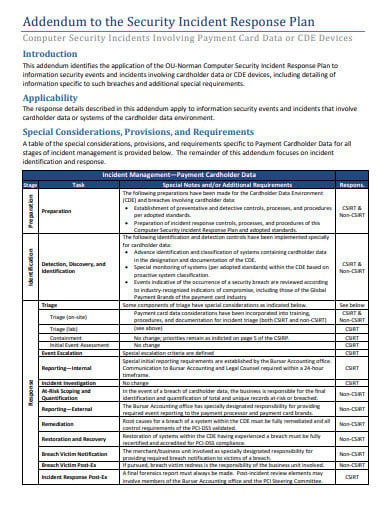 ou.edu
ou.edu8. Credit Card Security Incident Response Plan Template
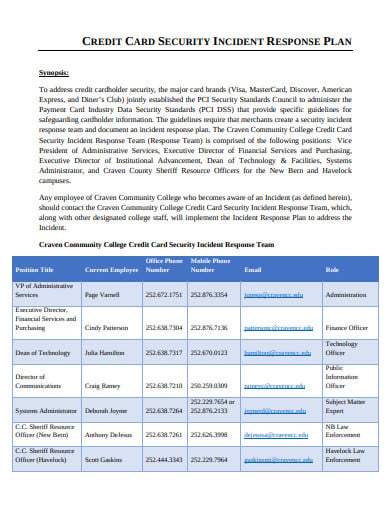 cravencc.edu
cravencc.edu9. Standard Housing Data Security Incident Response Plan
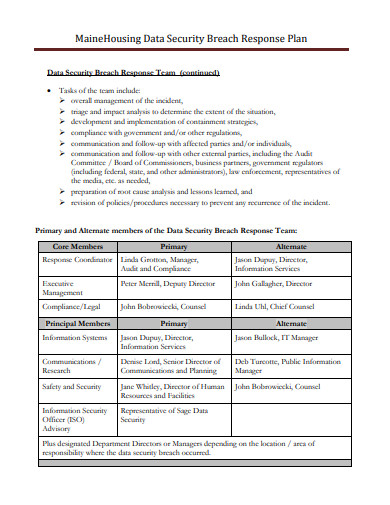 mainehousing.org
mainehousing.org10. Basic Security Incident Response Plan Template
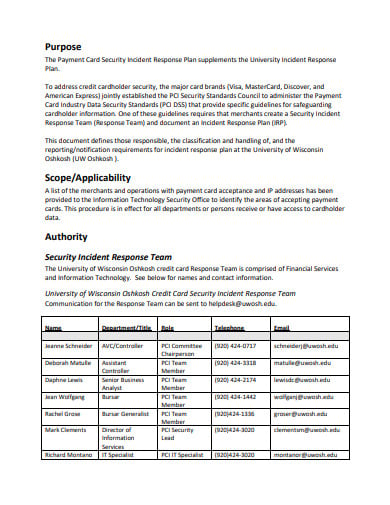 uwosh.edu
uwosh.edu11. IT Security Incident Response Plan Form
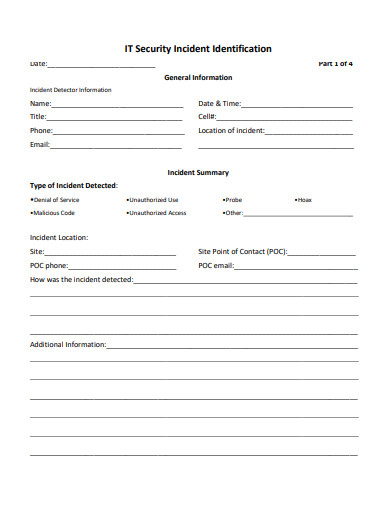 astate.edu
astate.edu12. Data Security Incident Response Plan Format
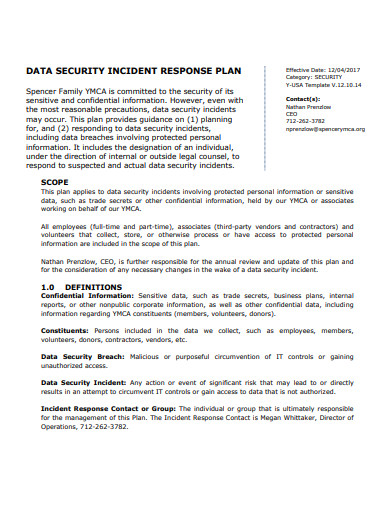 spencerymca.org
spencerymca.orgImportance of An Incident Response Plan
Incident response is the process of cleaning and recovery when a security breach is found. You can also see such breaches referred to as IT accidents, security accidents, or computer accidents-but whatever you name them, you need a strategy and a team committed to handling the incident and mitigating recovery damage and costs. Many companies call this unit the Computer Security Incident Response Unit (CSIRT).
Preparation
When the time comes your CSIRT needs to work like a finely tuned computer, and that takes effort. Defining a corporate security policy: this usually involves reasonable use of company data, penalties for breaches of security, and descriptions of what constitutes a security incident. Defines a step-by-step manual for how a security incident will be treated by the CSIRT including incident reports and internal and external correspondence.
Identification
Defines what conditions CSIRT triggers. It may be a particular problem such as “finding on the floor a random USB drive”. It could also be a composite collection of conditions that trigger the plan: an unexpected access warning combined with a warning about an irregular upload in the same hour to a cloud storage site might be a cause.
Containment
The danger is contained. There are two confinement types: long, and short. Short-term mitigation is an effective response that prevents the threat from expanding and causing further damage. Replacement on all affected devices for the later forensics to save their current state. Long-term mitigation involves restoring all systems to service to allow normal business activity only without the accounts and back doors that enabled the invasion.
Eradication
Establish a restore process for all affected systems. A strong starting point is to re-imagine all processes that are involved in the incident and erase all signs of the incident. These measures will include the specifics of your company’s licensed disk cloning program and photos. Finally, upgrade the safety systems to avoid a similar form of a security breach from occurring again.
Recovery
Determine how to return all devices to full production after ensuring they are clean and free of any nastiness that might lead to a new safety accident.
Lessons Learned
For training purposes, study the report of the incident with the CSIRT. Update the IR plan based on input, and any deficiencies found.
Roles in a Security Incident Response Team
- Incident Response Manager: The CSIRT team leader who manages the IR Strategy in practice.
- Security Analysts: The ground forces accountable for neutralizing the threat and preventing an active security incident.
- Management: The management team supplies the CSIRT team and the IR program with the tools and buy-in.
- Human Resources: If an individual is engaged, HR is also brought in to support the CSIRT efforts.
- General Council: Enforcement and legislation are an important part of data protection, so include the lawyers – even as part of a full-time team. You may also have a role performed by a full-time enforcement officer.
- Public Relations: PR can help handle messaging in the aftermath of an accident, particularly now that data breaches need to be so quickly public knowledge.
FAQ’s
What is a security incident response plan?
Incident response refers to a coordinated approach to handling and managing the consequences of a security breach or cyber-attack, also known as an accident involving IT, computer accident or defense. An incident response plan is a collection of guidelines to help IT workers track, react, and recover from incidents related to network security. Such kinds of plans tackle problems such as cyber crime, data loss, and regular work- service outages.
What are the five steps of incident response in order?
The five stages of readiness for emergency response include readiness, preparation is the secret to a successful response to an incident, reporting, and identification which focuses on tracking security activities to track, warn, and report possible safety incidents, analysis and triage, continuation and neutralization, and activity post-incident.
What constitutes a security incident?
A security breach is an occurrence that may mean that the systems or data of an entity have been breached, or that steps have failed to protect them. In IT, an event is something that has meaning to system hardware or software and an accident is an occurrence that interrupts regular activities.
What is the first step in security incident management?
The first goal is to organize by putting in motion a clear IR strategy in advance. Before a major attack or security breach occurs, the company will develop and battle-test a plan. It should deal with the following phases of response as described in the NIST Computer Security Incident Handling Guide.
What is incident recovery?
Incident management is an coordinated approach to handling and handling the consequences of a security breach or cyber attack, also known as an accident involving IT, computer accident or defense. The goal is to manage the issue in a way that limits harm and decreases the time and cost of recovery.






