Table of Contents
- Policy Template Bundle
- 5 Steps to Make a Security Audit Policy
- FREE 8+ Security Audit Policy Templates in MS Word | PDF
- 1. IT Security & Audit Policy Template
- 2. Information Security Audit Policy Template
- 3. Company Security Audit Policy Template
- 4. Advanced Security Audit Policy Template
- 5. Sample Security Audit Policy Template
- 6. Professional Security Audit Policy Template
- 7. HIPAA Security Audit Policy Template
- 8. Information Technology Security Audit Policy Template
- 9. Security Audit Policy Template in DOC
FREE 8+ Security Audit Policy Templates in MS Word | PDF
Initiating an effectual audit policy is an essential aspect of IT security. Tracking the creation or moderation of objects helps you mark potential security problems, certify user accountability and give authentication in the event of security holes. We have provided audit security policy templates below that you might want to use. Have a look at them and choose the best one for framing your policy.

Policy Template Bundle
5 Steps to Make a Security Audit Policy
Step 1: Describe Your Audit
Define the width of the audit. It means to note down the list of all your assets. Once you have a list of assets, you need to define your security perimeter. A security perimeter segregates your assets into two segments: things you will audit and things you won’t audit.
Step 2: Describe your Threats
Next, lay hold of your list of valuable assets and note down a similar list of potential threats to those assets. The most basic and common threats that you need to think about in this step are negligent employees, malicious insiders, malware, and so on.
Step 3: Determine Current Security Performance
Since you have your list of threats now, you need to be honest about your company’s capability to defend against them. At this note, you are assessing the performance of present security structures, which means you’re necessarily estimating the performance of yourself, your team, or your department.
Step 4: Hierarchize
Take your list of threats and measure the probable damage of a threat occurrence versus the chances that it actually can occur. Don’t forget to include the results of the current security performance assessment when scoring relevant threats.
Step 5: Prepare Security Solutions
The last step of your internal security audit is to take your classified list of threats and write down a similar list of security improvements and remove them.
FREE 8+ Security Audit Policy Templates in MS Word | PDF
1. IT Security & Audit Policy Template
 nsit.ac.in
nsit.ac.inA complete guide of security audit policy has been provided in the template here which you can take reference in order to spot security problems and monitor the modification of objects in your organization. Check it out once and go through it. If you consider it to be important then download the file now and can also check IT policy templates.
2. Information Security Audit Policy Template
 technology.wv.gov
technology.wv.govThe information security audit policy template provided here will enable to maintain an objective and internally independent Information Security Audit Program. The program will serve the Executive Branch by examining, evaluating, and reporting on IT applications, related systems, operations, processes, and practices to provide reasonable assurance to security controls. If you wish to create such a policy then take a look at the PDF file given here and download it. It will definitely ease your work and manage time.
3. Company Security Audit Policy Template
 omeka.org
omeka.orgIf you wish to create a company security audit policy then you might want to have a look at the sample we have attached here. It consists of steps and procedures which will enable you to help with the security-based situations in your company. Download the file now and get started. You can also check policy templates in pdf for more information.
4. Advanced Security Audit Policy Template
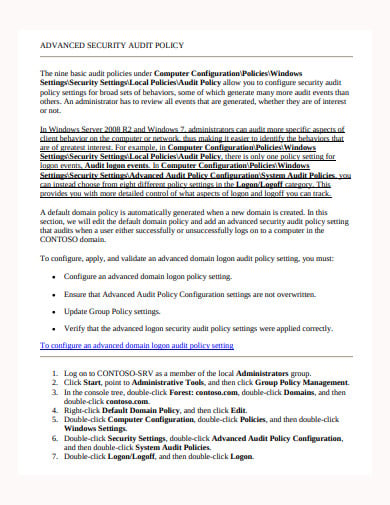 mcsa15.biz
mcsa15.bizAn advanced security audit policy allows you to configure security audit policy settings for broad sets of behaviors, some of which generate many more audit events than others. To get a brief description of the steps and procedures of the audit policy you need to check out the template provided here. You will find here what you are looking for and it will definitely enable you with all the help that is required.
5. Sample Security Audit Policy Template
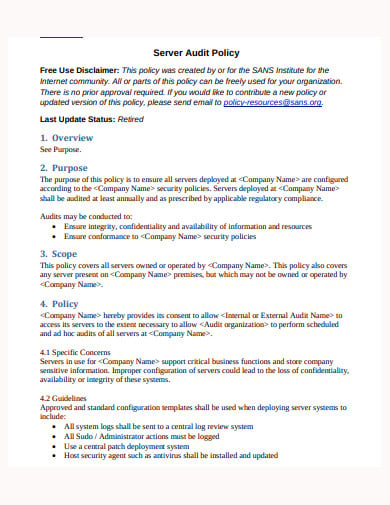 sans.org
sans.orgA basic security audit policy consists of an overview, purpose to ensure all servers are developed, configured and audited, scope, policy, policy compliance, definitions and terms and so on. To get hindsight on all the details grab the sample now. It is assured that your work will be done without much of a problem. Also click privacy policy templates for more details.
6. Professional Security Audit Policy Template
 semanticscholar.org
semanticscholar.orgDue to a lack of security conditions audits procedures are done. In order to make your task easy and hassle-free a study has been provided here based on the professional security audit policy. Get it now and design one for your company. It will help you improve the situations and enhance security levels.
7. HIPAA Security Audit Policy Template
 palmer.edu
palmer.eduIf you are looking for a HIPAA security audit policy then you are definitely on the right track. The policy which is given here includes all the necessary components like rationale, purpose, scope, definitions, administrative rules, audit responsibilities and much more. Dive into the details given here and make a complete use of it. You can refer to it as your guidance.
8. Information Technology Security Audit Policy Template
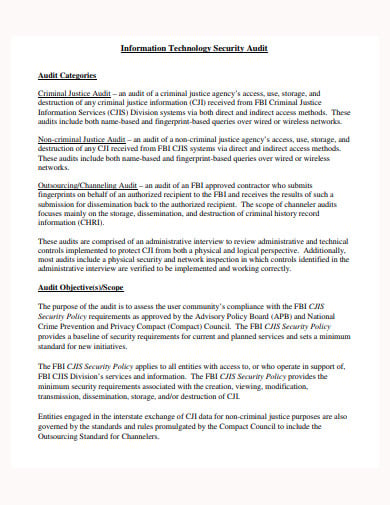 fbi.gov
fbi.govThere are various audit categories and procedures that you need to understand before you make an IT security audit policy by yourself. The example provided here will basically guide you and give you all kinds of the necessary information that you require. It can be all yours if you download it now.
9. Security Audit Policy Template in DOC
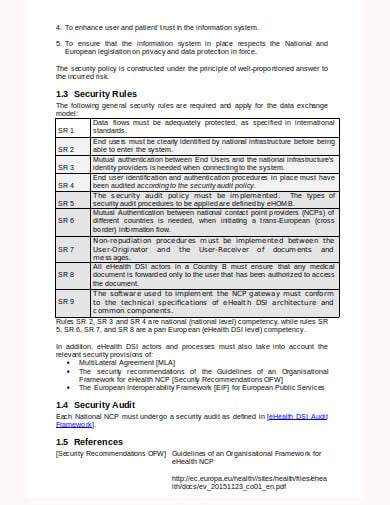 ec.europa.eu
ec.europa.euIf you want to know anything about the security policy, check out the Doc file we provided as an example here. Not only you can use the details as your reference, but you can also edit the file and modify it according to your needs. Have a look and after going through download it instantly.






