Free Compliance Register

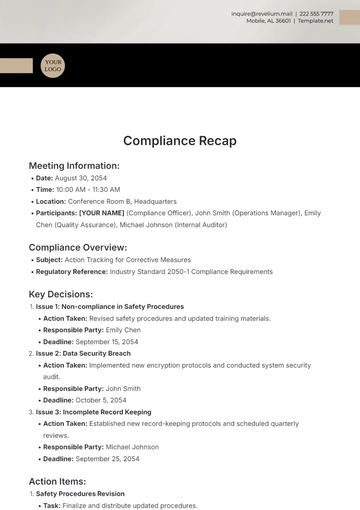
I. Incident Details
Date of Incident: April 15, 2050
Time of Incident: 10:30 AM
Location: Main Server Room, Building 1, Floor 5
Incident Description: An unauthorized individual gained access to the server room and attempted to tamper with the main server.
II. Involved Parties
Employee ID: 123 (Security Officer)
Contractor XYZ (Maintenance Staff)
III. Compliance Requirement
Relevant Regulation/Policy: General Data Protection Regulation (GDPR)
Specific Requirement: Protection of Personally Identifiable Information (PII) as outlined in Article 30.
IV. Severity Assessment
Severity Level:
Moderate
Impact Assessment: The violation posed a moderate risk of data breach and could lead to potential legal ramifications due to unauthorized access to sensitive data.
V. Root Cause Analysis
Primary Cause:
Lack of proper access controls in the server room.
Contributing Factors:
Inadequate employee training on security protocols.
System vulnerabilities in the access control system.
VI. Corrective Actions Taken
Immediate Actions:
Access privileges are revoked for the unauthorized individual.
Enhanced monitoring of server room access.
Affected data is encrypted for added security.
Long-Term Solutions:
Implementation of biometric access controls for the server room.
Mandatory security awareness training for all employees.
Regular security audits to identify and address vulnerabilities.
VII. Responsible Parties
Personnel Responsible:
IT Security Manager
Facilities Manager
Accountability Measures:
Performance evaluations for staff involved.
Mandatory completion of security training within 30 days.
VIII. Documentation and Evidence
Evidence Collected:
Access logs show unauthorized entry.
An incident report detailing the attempted tampering.
Documentation:
Security incident report.
Screenshots of access logs.
IX. Follow-Up Actions
Follow-Up Plan:
Conduct quarterly security audits of access controls.
Schedule monthly security training sessions.
Review Dates:
Quarterly security review meetings are scheduled for April, July, October, and January.
X. Approval and Sign-off

[Compliance Officer]
[Date]
- 100% Customizable, free editor
- Access 1 Million+ Templates, photo’s & graphics
- Download or share as a template
- Click and replace photos, graphics, text, backgrounds
- Resize, crop, AI write & more
- Access advanced editor
Efficiently manage compliance records with Template.net's Compliance Register Template. Easily editable and customizable, it provides a structured format for recording regulatory data. Accessible via our Ai Editor Tool, it simplifies compliance tracking, allowing seamless organization and retrieval of essential information.