Best AI Content Writing Tools
Introduction Creating content today is faster, smarter, and more competitive than ever. Whether you are a blogger, marketer, business owner,…
Jan 24, 2025
Owning a business in whatever type of industry or being put in charge of one means being part of an ever-growing and competitive market comes with a responsibility that has put even the most skilled, and experienced business leaders to the test, time and time again. Operational plans are that kind of plans that help management view their opinion through the perspective of an opposition. This way they will be able to study their protective efforts and its adequacy in protecting your organization’s information.

Looking to create a security operational plan to learn how to deal with risks and ensure your business’s success? Then you need to download this above-mentioned plan template and know all the necessary factors required for your security plan to be successful. Get organized, communicate better, and improve your business’s overall security with the aid of this template. Just download, edit and customize to suit your preferences perfectly.
Be clear and concise with your plans using this template to make the perfect plan you need. It is available in many file formats, that can be of great help to you in creating the right plan needed. All you would have to do is download the template, edit and customize it according to your preferences.
Being on top of a company’s operation, regardless of what industry you are in, making sure to keep everyone and everything in the premises of your organization safe and that there is enough security to protect it is very important. Check plan templates in PDF for more. Download this professionally-designed operational plan document for your company. This is high-quality and printable. It is also easy to edit and customize multiple software. Printable and free to download.
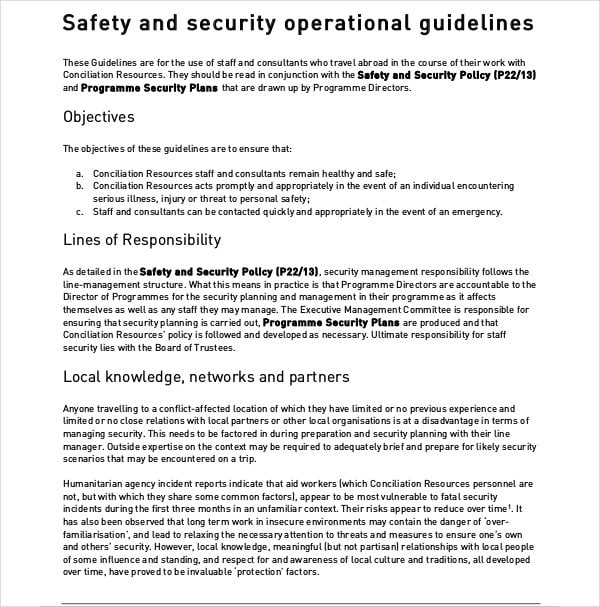
All of us privy to the country’s current situation, where getting killed with a gun, being on road accidents, and being the victim of fraudulent activities that rips companies off almost every last penny, is somehow the new normal. You may also see security operational plans. It’s almost as if the dark ages aren’t through with us just yet or it’s making quite a comeback, what with crime rate reaching figures the average American didn’t think was possible.
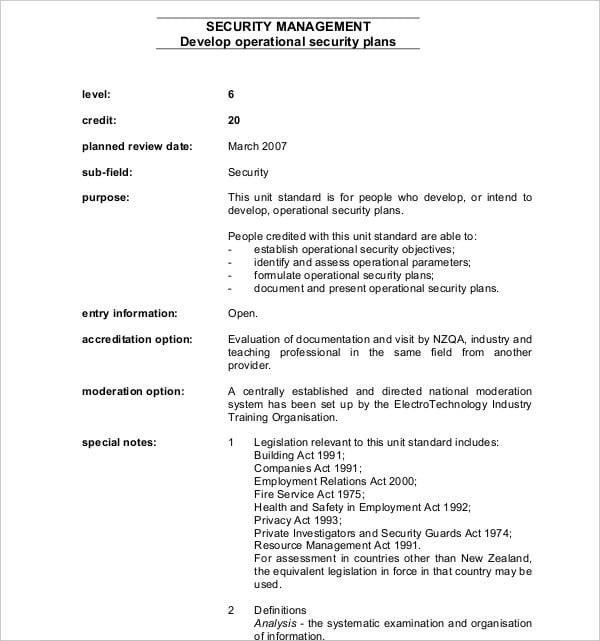
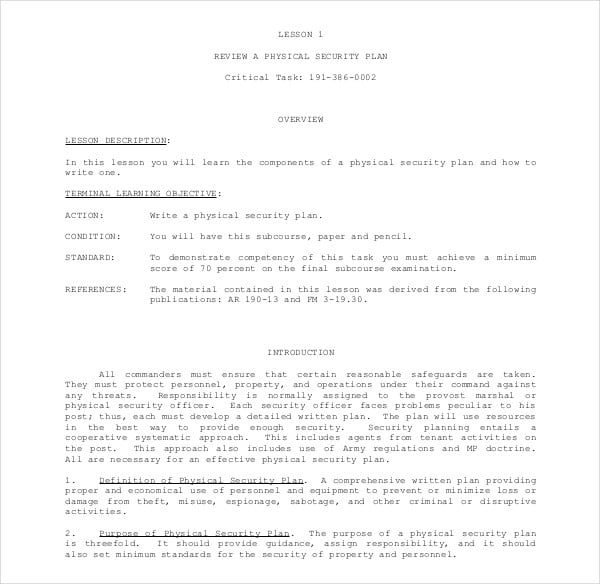
Operational security (OPSEC), also known as procedural security, is a process in risk management that seeks to encourage business owners and managers to see operations from the perspective of an “enemy” for the protection of sensitive data or information from being accessed by, and falling into hands that has every intention of harming the company by using its own strategies and information about products, marketing, plans and policies, all of which should be exclusive to the knowledge of the workforce and their leaders.
Although OPSEC was primarily used in the army, it is fast gaining well-deserved popularity among the private sector or in the corporate world. Things that fall under this include proper monitoring of people’s behaviors in the company, social media habits and it also aims to discourage employees from disclosing their system login credentials through SMS or email.
Today’s news revolves around mass shootings, burglaries in business establishments on top of theft of valuable trade secrets. Then you have to worry about vandalism by some gang members who thought to make a statement equates to spraying paint and drawing graffiti on private company property. Dealing with this, whilst making sure you’re hitting performance targets, can be overwhelming but not if you have a security operational plan in place, to implement the necessary and updated security and safety measures and keep all areas of your business protected especially sensitive information paramount to your business operations.
 nzqa.govt.nz
nzqa.govt.nz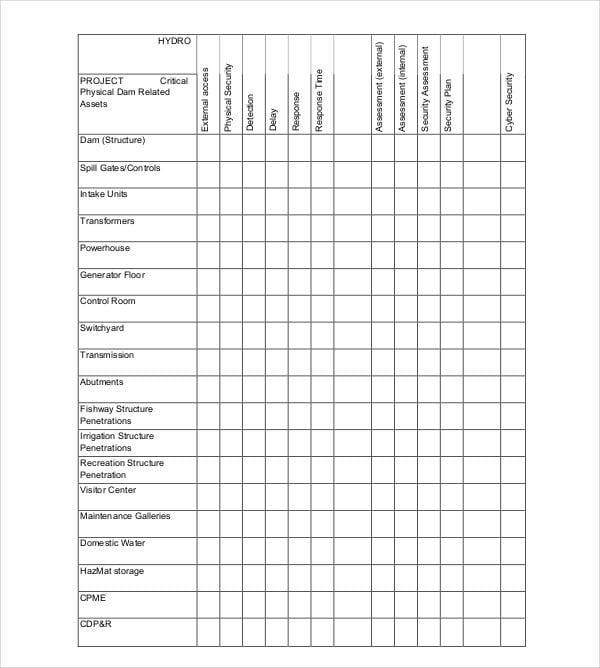 ferc.gov
ferc.gov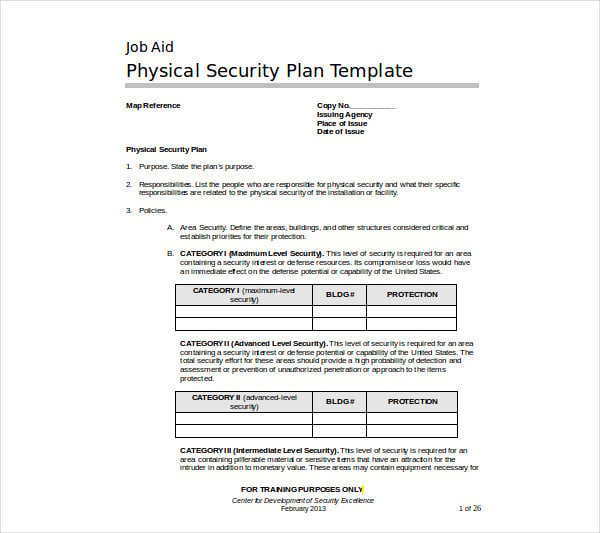 cdse.edu
cdse.edu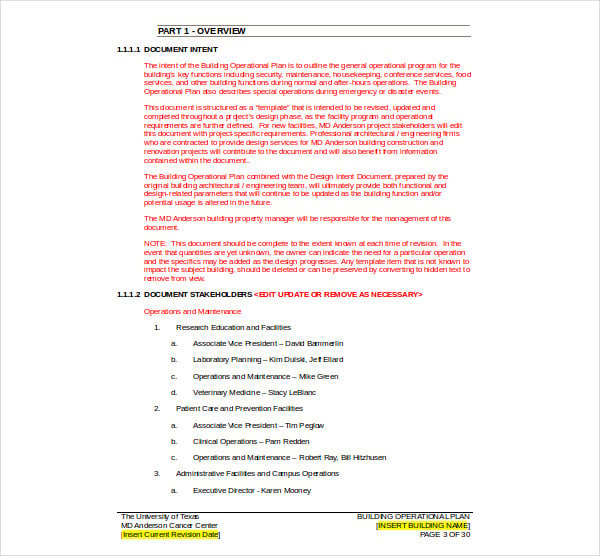 mdanderson.org
mdanderson.orgFor obvious reasons, the importance of safety and security in business cannot be emphasized enough. This means, it is imperative to come up with a strategy or security plan to ensure that there’s a working security system if the company cannot yet afford to have a control room for monitoring system activity. All over the work premises as well as having the right people behind them and in charge of both the employees’ and the building’s safety while it’s business as usual can be easily monitored. Businessmen shouldn’t wait until company data and sensitive files in the system are compromised until they employ risk management measures for security.
It should, therefore, be one of the company’s highest priorities to employ personnel who could man a security or control system or be in charge of the overall security just in case someone poses a threat through by training to gain unauthorized access through the building or the system being used. Check marketing plan templates for more. Also, you have to remember that it’s nearly impossible to recover stolen data if your adversary managed to check every nook and cranny of your system enough to get past it, undetected.
Some of the processes involved in implementing operational security can be broken down into these 3 steps:
This would include your product research and development and the company’s intellectual property obviously falls under this category too, as well as financial statements. Never forget that any form of financial data by any of your stakeholders, especially that of your customers, is considered confidential, otherwise, be prepared for lawsuits.
You should be able to identify the possible threats for all the parts of the information you think and consider sensitive. These need more attention as they can put the reputation of your company in jeopardy. Check event operational plan templates for more. This way, it gets easier for you to make decisions on how to curb the risks for further damage.
This is pretty self-explanatory because your operational security plan falls down to creating and implementing measures for removing threats and mitigating risks that were identified. HR operational plan templates that are available online can be of great help to you in creating the perfect HR plan for your organization.
 c-r.org
c-r.org sta.uwi.edu
sta.uwi.edu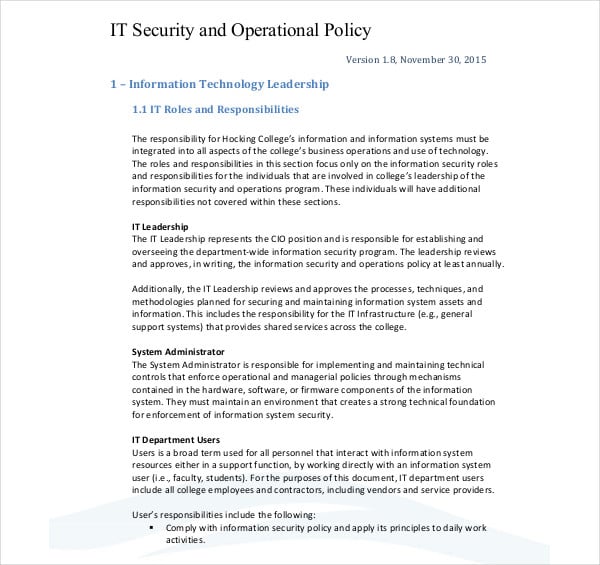
 downloads.slugsite.com
downloads.slugsite.comA company must not only have a operational strategy, but it should also have a lot of security measures and security risk management against any possible risk that they might have to go through. You can also check sample plan templates that are available online. It must also make sure that valuable information doesn’t end up in the wrong hands because of a building break-in or through unauthorized access to various company databases, networks, and files, etc.
Check incident response plan templates for more. If this happens, then the years and years’ worth of work and research dedicated to giving the business leverage over competitors just like any company determined to keep its place in the industry does. A company that doesn’t take operational security seriously might have a lot of trouble later, as this may cost them everything they have build till now.
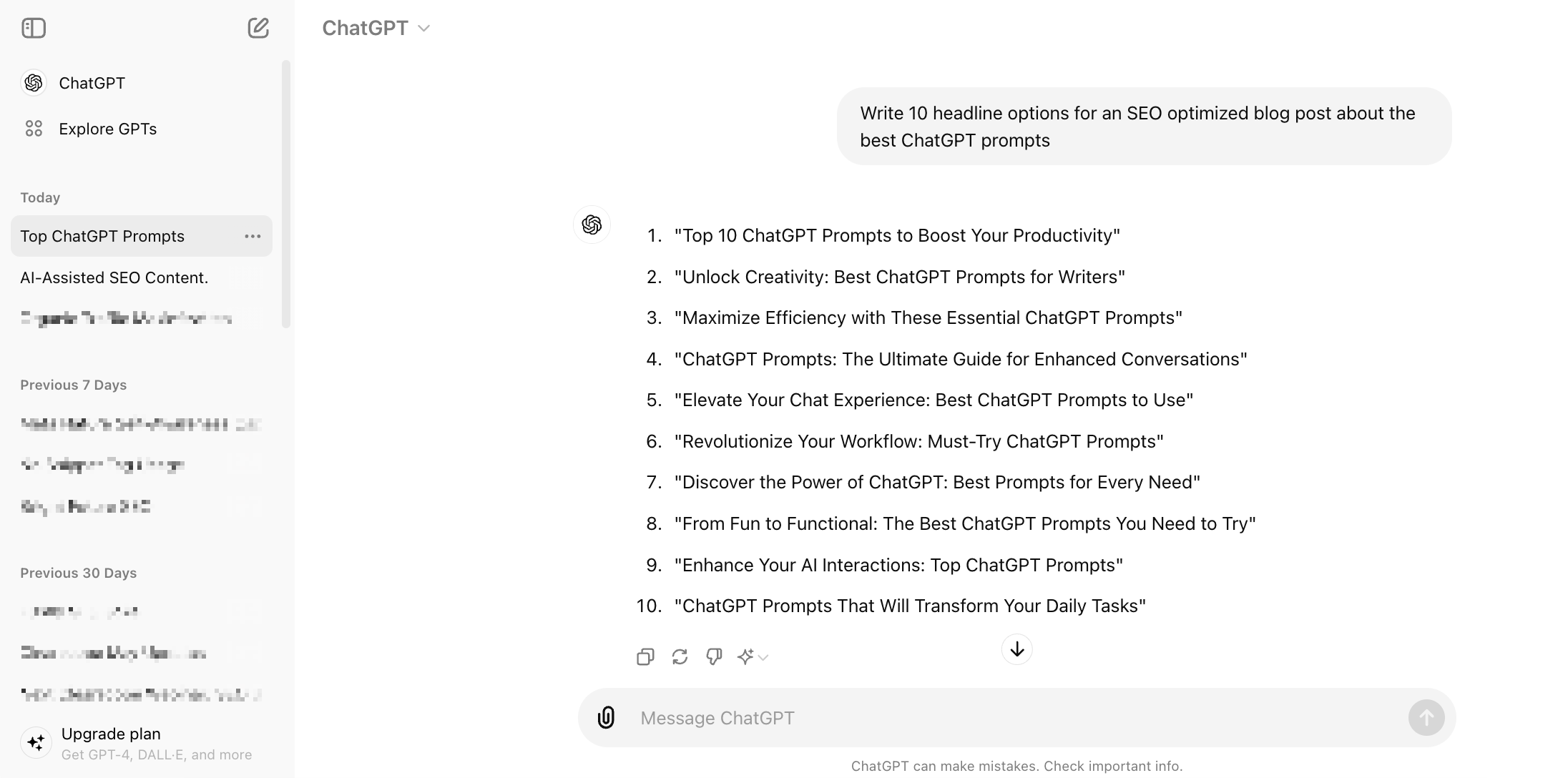
Introduction Creating content today is faster, smarter, and more competitive than ever. Whether you are a blogger, marketer, business owner,…

1. Introduction: The Real State of AI Image Generation in 2026 AI image generation in 2026 is no longer a…
Introduction: The State of AI Customer Service in 2026 Customer service has undergone a fundamental shift. By 2026, AI chatbots…
Introduction: AI Video Generation Is No Longer Experimental What began as short, unstable demo clips has evolved into production-grade systems…

In today’s fast-paced digital world, efficiency and consistency are key to content creation, and this is where the power of…
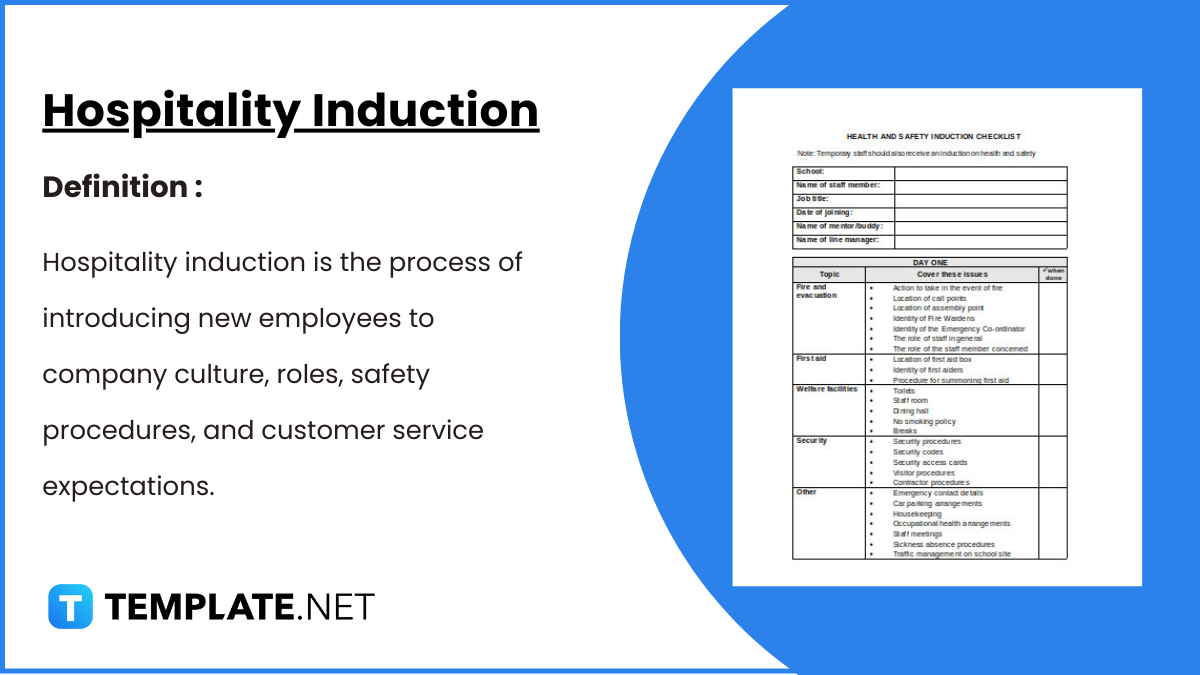
Hospitality Induction Templates are structured guides created specifically for the hospitality industry to facilitate the onboarding process for new employees.…
Whether you are a business or an organization, it is important for you to keep track of your business bank…
A Company Description provides meaningful and useful information about itself. The high-level review covers various elements of your small business…

A smartly designed restaurant menu can be a massive leverage to any food business.