
11+ Remuneration Policy Templates in PDF | Ms Word
Arrangements on a remuneration policy are significant reports made by associations crosswise over different fields for giving standards to moral…
Sep 03, 2024
A confidentiality policy implies individual correspondence or data identifying with an association’s business that is obscure to general society and just shared between a couple of individuals. This data comes into the ownership of the Organization through its work.

 councilofnonprofits.org
councilofnonprofits.org nhs.uk
nhs.uk communitysouthwark.org
communitysouthwark.org endabusepwd.org
endabusepwd.org lccare.org
lccare.org cmegroup.com
cmegroup.com nhs.uk
nhs.uk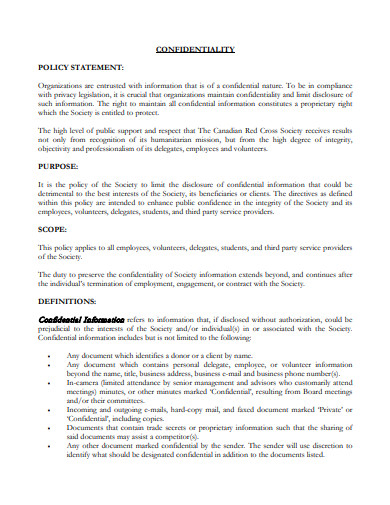 redcross.ca
redcross.ca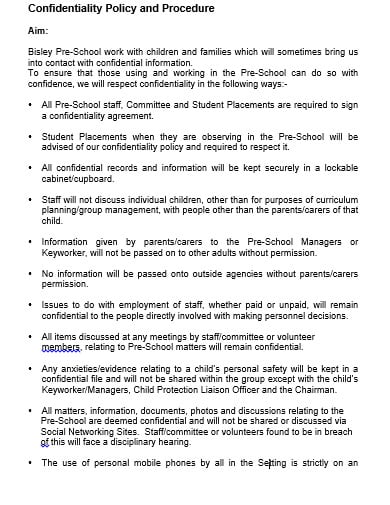 school.org
school.orgThe Organization perceives that events may emerge where singular laborers feel they have to break the secrecy. Classified or touchy data identifying with an individual might be revealed where there is danger of a threat to the individual, a volunteer or representative, or the general population everywhere, or where it is illegal to retain it. For instance, data might be unveiled to outside offices, for example, the police or social administrations. Find more privacy policy templates by visiting this link. Where a specialist/worker feels privacy ought to be ruptured they should raise the issue quickly with their Line Manager who will examine the alternatives accessible and choose whether secrecy ought to be broken.
A representative or laborer who wilfully ruptures these privacy rules will confront disciplinary activity under the Organization’s disciplinary techniques. The rupture or breaks may establish potential gross offense which may bring about rejection and legitimate activity.
The arrangement is official on people significantly after they have left the Organization’s business.
All current and new representatives and laborers will be made mindful of this classification approach through enlistment and further preparing. View a wider selection of restaurant policy templates right here.
Foot Note:
The Confidentiality Policy could likewise express that the accompanying provisions be remembered for any privacy or non-revelation understanding (presently regularly utilized in business) between the Organization and an individual from its staff, planned for ensuring data and determining explicit uses for unveiled data. This may be essential where touchy data should be shared and would give legitimate cures if there is any arrival of classified data.
A non-contend condition, disallowing the beneficiary of the data from beginning a contending organization or unveiling secret data to a contender. Explore a variety of leave policy templates here.
A non-request condition, disallowing the beneficiary from poaching representatives from the Organization.
On the off chance that a business wishes to incorporate these conditions, lawful exhortation ought to consistently be looked for. The two provisos will be time-restricted.
Some Council staff may approach business data, understandings or agreements. This data must be treated as secret, and just examined/unveiled where this structure some portion of the representative’s transmit inside the association. Staff ought to counsel their director if they are in any uncertainty.
Access to secret data or mysterious information might be looked for research, review or checking purposes, either by other board zones or by outside associations or open bodies.
Inward demands identified with inquiring about tasks must be affirmed and proper accommodation will be required.
The Police don’t have programmed rights to individual data held by the Council about help clients. The issue ought to consistently be alluded to a supervisor as well as the Data Protection Officer/Legal Services.
While the general rule is that data got about kids and their families must be imparted to them and not with others, there are special cases. People in general enthusiasm for protecting the welfare of kids abrogate the general population enthusiasm for keeping up privacy and the law allows the divulgence of private data where this is important to defend a kid or kids. Successful data sharing supports coordinated working and is an indispensable component of both early mediation and defending. Check out more professional policy templates available here.
Exposure of secret data ought to be legitimate for each situation, for instance, to give data to experts from different organizations working with the kid, and where conceivable and fitting, the understanding of the individual concerned ought to be gotten.
The conditions wherein data held in records on youngsters and families can and ought to be uncovered and imparted to others with or without assent are set out in the accompanying areas.
In every single other case, where outsiders, for example, promoters, specialists or outer analysts demand access to data, this should possibly be given whenever composed assent is given by the individual concerned or if a Court Order requires it. Looking for more insights? Dive into our blog post about templates here template.net.

Arrangements on a remuneration policy are significant reports made by associations crosswise over different fields for giving standards to moral…

Grooming policy is the rule or the protocol that an employee has to follow when he becomes the employee of…
A dress code policy is defined as a set of guidelines to make it easy for the employees to know…

A sales commission policy fulfills the policy of establishing responsibilities for setting commission rates and to define the point at…

A confidentiality policy implies individual correspondence or data identifying with an association’s business that is obscure to general society and…

The dividend policy is a financial decision that indicates the balance of the firm’s wages to be paid out to…

The payment policy is the set of rules or directions that guides a customer to make the bill payment templates.…
Bonus Policy can be referred to as the protocol formulated in an organization based on which the employees are given a…
Recruitment policy is the practice that a company exhibits while hiring employees. It a statement that outlines the rules and…