Table of Contents
- FREE 7+ Security Configuration and Analysis Templates
- 1. Security Configuration and Analysis Windows
- 2. Security Configuration Analysis Framework
- 3. Security Configuration and Analysis Technology
- 4. Security Configuration Management Analysis
- 5. Security configuration Administration Analysis
- 6. Security Configuration Program Analysis
- 7. Security Configuration Commands Analysis
- 8. Security Configuration Automated Analysis
- 5 Steps to use the Security Configuration and Analysis
- FAQ’s
- How does the Security Configuration and Analysis?
- Why is this necessary in storing in the databases?
- Why is it important to have the Security Configuration and Analysis?
FREE 7+ Security Configuration and Analysis Templates in PDF
The Security Configuration and Analysis is the snap-in tool that the users can utilize one or more saved configurations to the database. Importing configurations establishes the machine-specific security databases that save the composite configuration. You can apply this composite to the computer system and analyze the proper system configuration against the stored composite configuration stored in the database.

FREE 7+ Security Configuration and Analysis Templates
1. Security Configuration and Analysis Windows
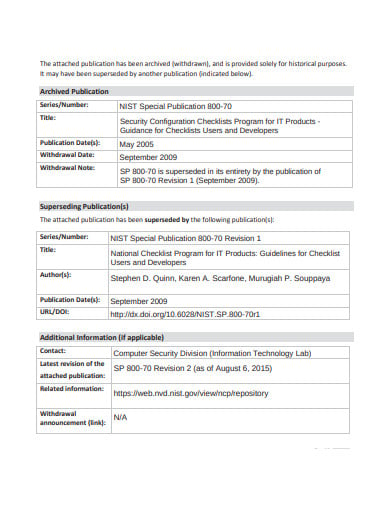
 ittoday.info
ittoday.info2. Security Configuration Analysis Framework
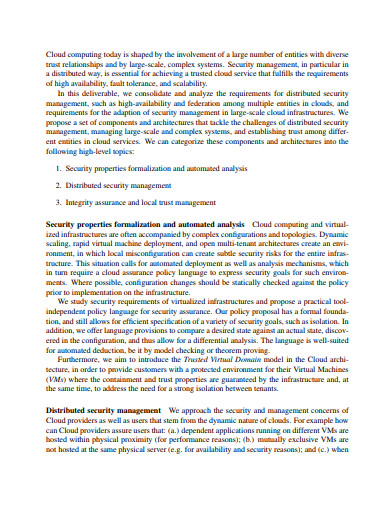
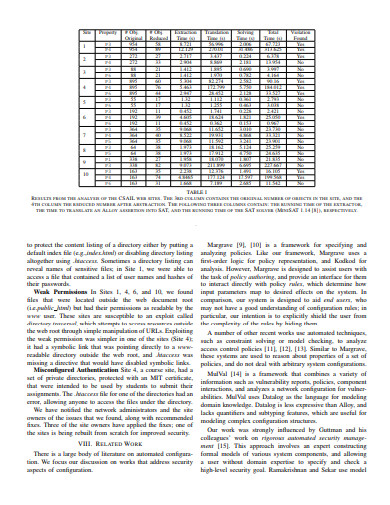 github.io
github.io3. Security Configuration and Analysis Technology
 psu.edu
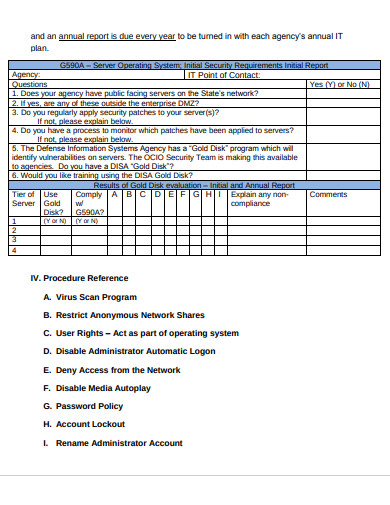
psu.edu4. Security Configuration Management Analysis
 fdicoig.gov
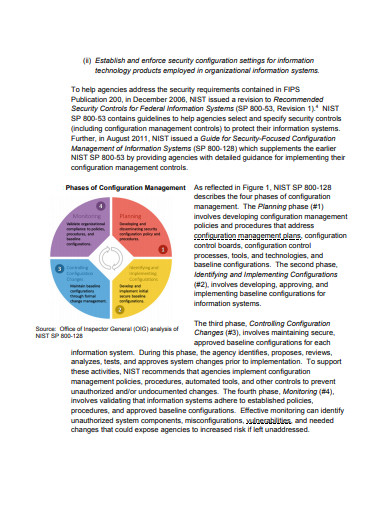
fdicoig.gov5. Security configuration Administration Analysis
 publishers.com
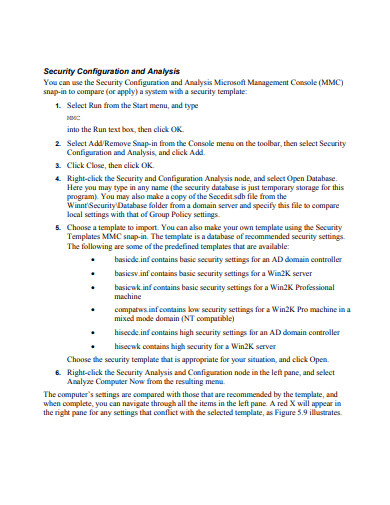
publishers.com6. Security Configuration Program Analysis
 govinfo.gov
govinfo.gov7. Security Configuration Commands Analysis
 fs.com
fs.com8. Security Configuration Automated Analysis
 schunter.org
schunter.org5 Steps to use the Security Configuration and Analysis
The security configuration is the snapping tool that the users can use to define the computer independent security configurations. These configurations are saved as text based.inf files and data. It is for analyzing and configuring the local system security. The position of the operating system and the apps on the device is dynamic.
Step 1: Click on “Start” menu and choose “Run”
First, open the system and click on the start button and search for the “run” and there you have to search for the rest of the directions. This is the first step in the entire progress of the configuration and analysis. You should follow the direction mentioned in the process one after the other to complete it.
Step 2: Type “mmc”
Here the extension of “mmc” must be mentioned in the search bar of the run and with this, we shall proceed to the next step. Without completion of this step, one cannot complete the next following step as they are all related to one other.
Step 3: Click on the”console” menu
After typing the “mmc” then press the return. The Microsoft management console opens and click on the console menu and choose the Add /Remove Snap-in… These things need some knowledge of the computer and if anyone with no idea uses it might end up crashing the computer system. So, better to follow them under expert supervision.
Step 4: Scroll down and click on Security Configuration
Then opens up the Add standalone snap-in option. Scroll down the options and choose the security configuration and analysis snap-in and then click on the add button.
Step 5: Click on “close” and “OK” button
Then you must follow the instruction on the screen that clearly indicates the “add and close” button. Then click on the close button and then the “ok ” button.
Step 6: Click right on “Security configuration” and type in any name
Here click on the the security configuration and analysis node and choose the option of the “Open the Database” from it and type in any name for the security database.The security database is the temporary storage for the particular program.
Step 7: Choose the template to import
After the user has the name for the program and then click on the”Open” button. Then choose the security template to import. You must keep in the mind that you can make your own templates. And in this way, you can easily configure the system for all the local computers.
FAQ’s
How does the Security Configuration and Analysis?
The Security Configuration and Analysis is used to directly configure and analyze the local system security. With its use of the private information, you’ll simply import the safety templates that square measure created with the safety templates and apply these to the native computers.. These will configure the system security with the levels specified in the template. There are different areas where the security templates are used to define the account policies, password policies, Account Lockout policy, etc.
Why is this necessary in storing in the databases?
The state of the operating system and apps on the device are dynamic. For an eg: you may need to change the security levels so that you can immediately resolve the administration or the network issues. However, this change can often go unreserved. This means that the computer is no longer meets the requirements for enterprise security. Regular analysis and security will help you to track the adequate level of security in each of the computers as part of the risk management program.
Why is it important to have the Security Configuration and Analysis?
These days the matter related to security is in everyone’s mind as well as on the computer screen. Every time you open the system, the security alerts pop-up every now and then like your emails, your anti-virus software, your network settings, and also the other apps. But searching every nook and corner can be a full-time job. Hence, the software company produces the comprehensive security configuration and analysis tool.






