4+ Security Gap Analysis Templates
To be able to have the place where you can take the plans and steps to attain the goal of having your security measures be in place where they should be and meet its standards, security Gap Analysis Templates will show you if you need additional items or process so you can have the goal of a protected place where you are working or living.

It is usually composed of multiple areas where it covers the personnel, material and protocol of certain to keep the order in its place. you may also see Analysis Templates.
Security Gap Analysis Template
Information Security Gap Analysis
 ehcca.com
ehcca.comInformation security gap analysis can bring clearance to any problems brought about by human or equipment ineffectiveness that affects the process of a company. It is an evaluation tool that can compare the desired performance of a company to their recent performance when it comes to their technological service or product. It can show the gaps from it which must be deal with immediately. You can also see Word Gap Analysis Templates.
Cyber Security Gap Analysis
Security and protection is assured in the systems of the different companies when you have a cyber security gap analysis. It is important to know about cyber and hacker strategies, it can be well discussed as identified barriers in the security system in the software and information technology where you create on how to prevent that to happen in the present and in future operations.
Safety & Security Gap Analysis Checklist
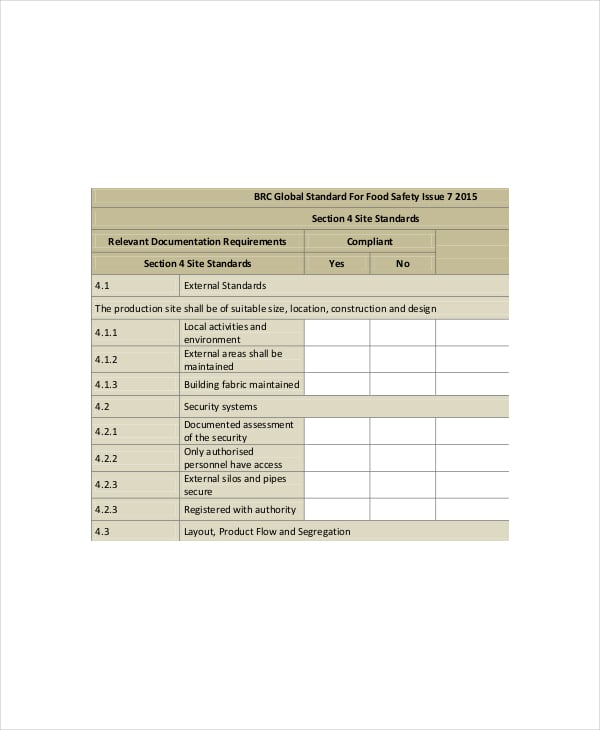 brcfoodsafety.com
brcfoodsafety.comThis checklist is based on the setup or requirement of an individual or group to say that any place, equipment or system is secured. There are factors that must be considered whenever this checklist is used as it has things to study upon and categories that cover the whole setting of any facility or firm if they comply with the security measures required to them. You can also see Competitive Analysis Templates.
Physical Security Gap Analysis
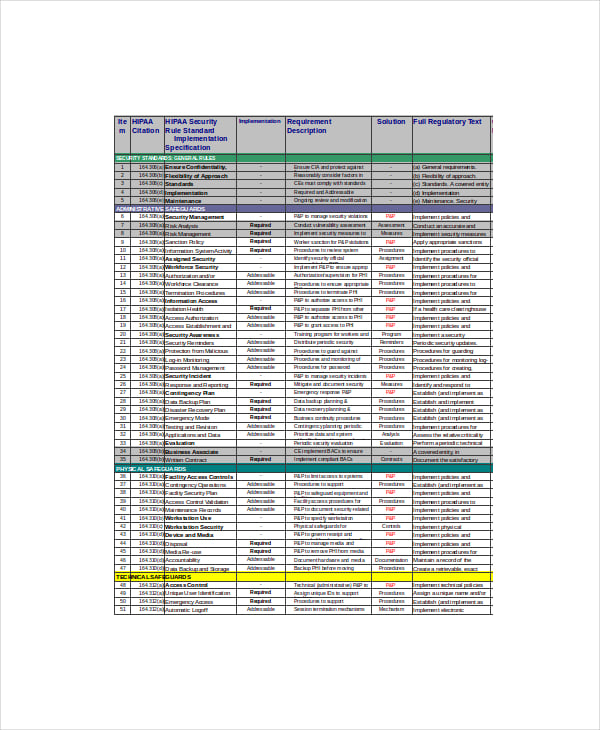 med.upenn.edu
med.upenn.eduPhysical security for a staff, employee or individual is the main and primary focus as physical security gap analysis is established. It is mostly seen in every business and company concerning the welfare and protection of each person involved. Creating an analysis form will assist the management to determine the gaps for improving the security of every personnel.
Social Security Gap Analysis
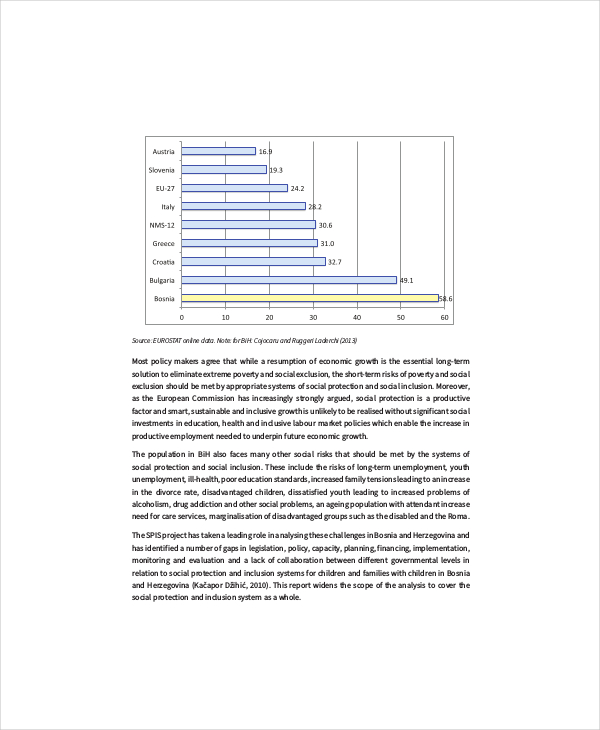 unicef.org/bih
unicef.org/bihMarket Gap Analysis
In the trades today, any investors of any business can help make a better decision to their stakes by using market gap analysis where they can compare which of the goods can have more profit than the others by improving its qualities or the company that creates it; the evaluation tool where the unique characteristics of a company must be met by their personnel to excel in their business.
> Target Readers and Users of Security Gap Analysis Template
This era always poses risk of harm to anyone and even privacy can also be broken in just a second. Security gap analysis is a tool you can rely when you are about to take this risk seriously and you don’t want unnecessary things to happen to you or to people around you. The providers of this security gap analysis will be those working and engaging in promoting and maintain security. You can also see Healthcare SWOT Analysis Templates.
> Advantages and Benefits of Security Gap Analysis
Security gap analysis will take your plans closer to what you want to have when it comes to protecting the people around you and even yourself from any danger or trouble. The evaluation of your security measures so you will not miss any missed spaces that can leave you vulnerable.
> Steps in Creating Security Gap Analysis
Have a performance evaluation of your security measures in your hand and put a comparison table of where you are now to what you want to be in the future. Then tally the plans you want to take in order to stick with the standards you have set in assuring security of your place. You can also see Budget Analysis Templates.
> Tips
Ask advice and consultation from any security personnel or group that can provide you the plan you are sure enough that are valuable.
The whole document can be downloaded and printed in Microsoft word, excel and pdf file. Users can then apply the whole format of the document in their work which can help them set up the proper security plan.