4+ Sample Security Gap Analysis Templates
To make your place a better place to live where anyone can move freely and do their business without disturbing your mind for any trouble that might happen, then security Gap Analysis Templates can take your plan to a higher level. There are steps to be taken in order to make sure that the security is being kept at all times that can be provided by this analysis report for you to follow strictly; any personnel and even equipment will be filtered with this report to have their performance be in line in any security task. you may also see Analysis Templates.
Sample Security Gap Analysis Template
Sample Network Security Gap Analysis
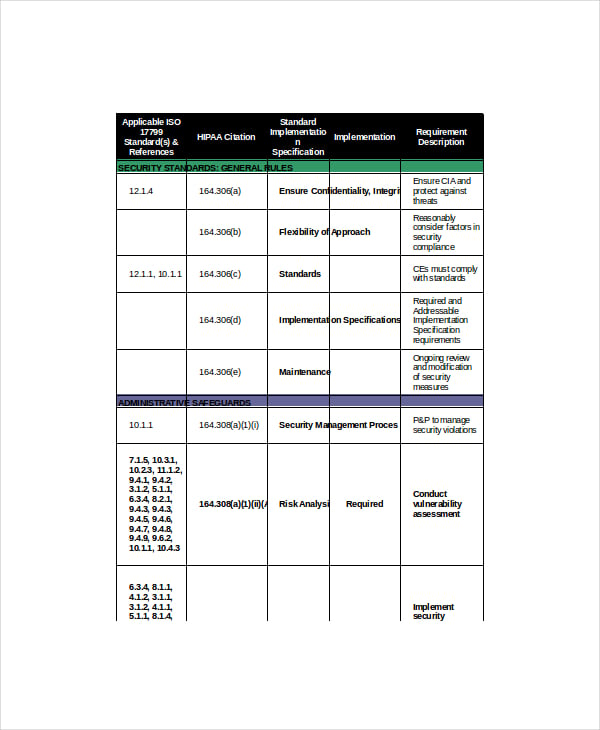 med.upenn.edu
med.upenn.eduTo make sure that you are doing well with your precautionary activities to protect your computer data and status from any breech or viruses from ruining your online profiles and documents saved in it, network security Gap Analysis Templates will evaluate your activities to keep the solitude, even the integrity of your computer and antivirus programs activity to avoid any cyber-attacks to your personal files.
Security Policy Gap Analysis
 all.net
all.netThis era always poses risk of harm to anyone and even your privacy can also be broken in just a second. Security policy gap analysis is a tool you can rely when you are about to evaluate any rules that is design in protecting any person or property and you don’t want unnecessary things happen to you or to people around as caused by the incompetence of these laws.
Sample Information Security Gap Analysis
 ehcca.com
ehcca.comExample Social Security Gap Analysis
 unicef.org
unicef.orgExample Information Technology Security Gap Analysis Template
Any measures that is taken to see if any technological device or program will help to make any work faster while checking the protection from any contents it will be handling is a prerequisite to be in observance of a high quality service and product. Information technology security gap Analysis Templates can help any company to verify the system or program they have is capable of defending itself of any threats from any sources.
> Target Readers and Users of Security Policy Gap Analysis
Responsible policy makers and security personnel will have this in their side when they want to have their task be congruent to the activities in having the security implemented in their place. It can be applied in a facility, personnel and even in cyber security where the wellness of the people using it will be in top priority at all times.
> Advantages and Benefits of Security Gap Analysis
When you have this analysis tool, you will no longer problem the risks that may face you of trouble. Its main concern is having new protocols and group that will take the job in carrying out security measures in their place.
> Steps in Creating Security Gap Analysis
Look for the set of rules established to have a secured place or property, and then have it compared to the actions that are done. You can choose a computer program that will assist you in carrying out this task. You can also see Skill Gap Analysis Templates.
> Tips
You can look for references that can give you guide in any security evaluation like those in police department and websites online.
You can take your task well in sample format of the document which can help you identify the previous and unseemly valuable in maintaining security in your place. You can use instantly its format so you will no longer look for numerous layout that can bring disorder in the appraisal process.