10+ Sample IT Risk Assessment Templates
Amid the growing complexities of the world, information technology is now considered as a crucial factor. Almost every inch of the societal structure depends on it be it for business, educational, religious, political, governmental, social, and other related purposes. Because of this, it is important that your data storage is protected and secured.

Given that man-made or natural disasters are somewhat inevitable, IT Risk assessment is a must in every institution. To help you understand and grasp an idea about it, you can start scrolling down and check out our offered templates for you. Furthermore, if you are looking for Project Assessment Template samples, you can also check out our listed templates.
Bank IT Risk Assessment Template

univie.ac.at
IT Project Risk Assessment Template
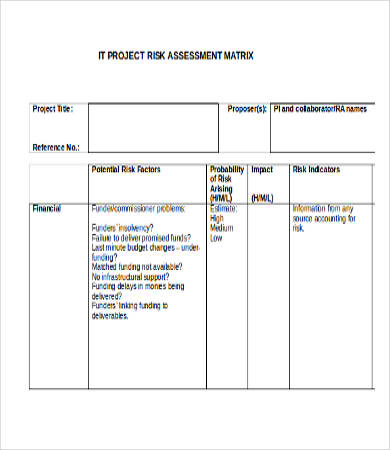
open.ac.uk
Enterprise IT Risk Assessment Template

citadel.edu
IT Infrastructure Risk Assessment Template
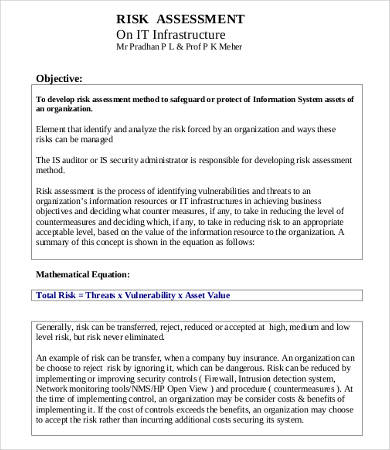
leetupload.com
IT Audit Risk Assessment Template

denvergov.org
Downloadable IT Risk Assessment Templates
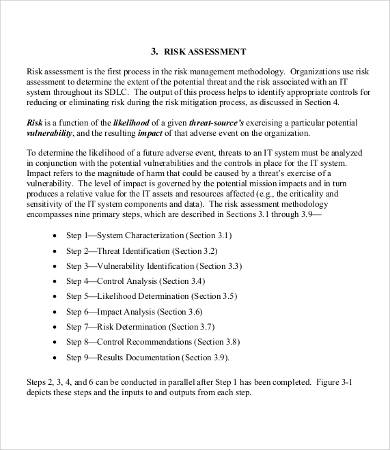
The basic purpose of a risk assessment—and to some extent, a Network Assessment Template—is to know what the critical points are in order to know what are solutions to help mitigate the adverse effects of unforeseen events like server crashes, power outages, and “acts of God.” To help you draft your risk assessment documents, here we offer some of these templates:
- Bank IT Risk Assessment Templates
- IT Project Risk Assessment Templates
- Enterprise IT Risk Assessment Templates
- IT infrastructure Risk Assessment Templates
- IT Audit Risk Assessment Templates
- IT Application Risk Assessment Templates
- IT System Risk Assessment Templates
- IT Risk Management Assessment Templates
Risk assessment is needed regardless of the size and purpose of a certain institution. For instance, a bank risk assessment is needed because the modern banking systems characterized by a fairly complex network of mutual credit exposures is still not infallible as what was emphasized in some of our templates.
The increase in technological interdependence between structures and institutions makes it more critical to conduct a risk assessment. In this way, IT professionals are given the opportunity to identify what may be the possible threats and risks the organization’s system may have in the near future. They can come up with ways and means to prevent a widespread damage and preserve the continuity of the transactions.
IT Application Risk Assessment Template
csrc.nist.gov
IT System Risk Assessment Template
hhs.gov
IT Risk Assessment Report Template

arctic-intelligence.com
IT Risk Management Assessment Template

isaca.org
IT Risk Assessment Process Template

security.vt.edu
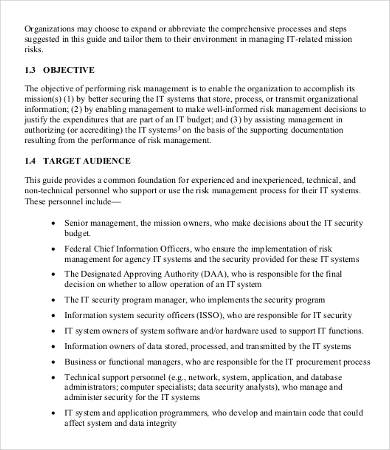
Points to Know about IT Risk Assessment
In all risk assessment and management processes, there are no definite rules and formats. It largely depends on the institution’s system of priorities and goals. If you’re an institution that values security and invests more on disaster management, then the process will definitely bring both success, security, and resilience not just for you but also for the people you manage and deal with.
Research studies point the importance of hazard identification in order to know if your company can withstand from possible damages. It is a matter on investing risk assessment and management in order to have a faster and resilient recovery in the future.
The common features of an IT risk assessment document are the following:
- Hazard identification. In the field of information technology, hazard identification could mean which system is basically prone for hacks, malware infections, data leakage, and other specific IT- related damages.
- Evaluation of risks and deciding control measures.
- Recording of findings.
- Implementation and occasional updates.
These are just some of the features, but they can vary because each organization faces different issues. Always ensure to pattern your assessment to your own specific issues and needs. Moreover, we also have Skills Assessment Template samples, if you’re looking for them. Just click on the link to access them.






