Table of Contents
- 5 Steps to Assess IT Security Risk
- 10+ IT Security Risk Assessment Templates
- 1. IT Security Risk Assessment Policy
- 2. IT Security Risk Assessment Template
- 3. IT Security Risk Assessment Plan Template
- 4. Common IT Security Risk Assessment Template
- 5. Corporate Security Risk Assessment
- 6. Recommendation IT Risk Assessment Template
- 7. IT Security Risk Assessment in PDF
- 8. Professional IT Security Risk Assessment
- 9. Quantitative IT Security Risk Assessment
- 10. Fundamental IT Security Risk Assessment
- 11. IT Security Self and Risk Assessment Template
10+ IT Security Risk Assessment Templates in DOC | PDF | XLS
When you are running a business, there are a lot of potential dangers and risks at a given time that needs proper management. If these risks are not assessed and managed properly at the correct time, then they could prove fatal to the business. IT security risk is referred to all those potential dangers that arise in the information and technology department of the organization. These risks are generally related to using IT resources. IT Security Risk Assessment Templates help in the analysis of these risks for their proper management.

5 Steps to Assess IT Security Risk
Five basic steps should be followed to assess IT risks:
Step 1: The Identification
The first step in the process of the assessment of IT risks, you first need to understand what constitutes IT risks. IT risks are those issues and concerns that are raised related to the use of information and technology in the organization. Once you understand this concept, you need to proceed to the identification process. This process involves identifying all the important IT assets of the company. After you have identified that, you need to prioritize the assets.
Step 2: The Anticipation
The next step of the process is to anticipate the potential threats of the company. These threats can be both internal as well as external. The internal threats involve those dangers that arise within the organization and can be put under check. The external threats of the company involve those risks that arise outside the organization and are generally outside the control of the organization. You need to anticipate these threats before moving on to the next step.
Step 3: The Assessment
The third step of the process is to do the assessment. For this, you need to refer to the two lists of risks you have made earlier. First, refer to the list where you have noted down the various IT assets and their risk, and compare it to the internal and external threat list. You need to consider each asset and risk individually carefully. Accordingly, the assessment also needs to be done individually.
Step 4: The Mitigation
When you are finished with the assessment of the risks, you can proceed to the mitigation step. In this step, you need to refer to the assessment results you got. Based on these results, you need to develop a plan or policy to mitigate the risks. The best tool for this task is a security policy. The security policy helps to establish rules and regulations that ensure the safety and security of all the assets of the company.
Step 5: The Prevention
The final step of this process is to make a prevention plan. This plan needs to be made keeping in mind the assessment results and the mitigation plan. The prevention plan will help to ensure that there are no such risks in the future. And if such risks arise, the prevention plan must highlight steps that should be taken to mitigate those risks.
10+ IT Security Risk Assessment Templates
1. IT Security Risk Assessment Policy
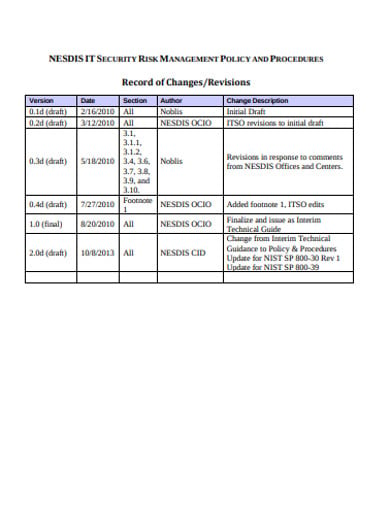 nesdis.noaa.gov
nesdis.noaa.govThe IT security risks refer to those problems that arise or could arise from the use of information and technology in an organization. The assessment policy for this is put in place to ensure that the risks are managed properly in time. If you want to make such a policy for your organization, then you need to download this IT Security Risk Assessment Policy template.
2. IT Security Risk Assessment Template
 rsa.com
rsa.comRisk assessment is one of the most important skills that need to be possessed by all employees. Such risk assessment is especially needed for IT risks as they require more attention. You can assess your organization’s IT risks with the help of this risk assessment template. This template has been created solely for this purpose.
3. IT Security Risk Assessment Plan Template
 oit.colorado.edu
oit.colorado.eduSecurity risks, no matter of what kind, are very important to be properly managed and assessed. For IT risks, a security risk assessment plan helps to make things easier. And this security risk assessment plan template is here to make the process of making this plan easier for you. All you have to do is click on the download icon and you are good to go.
4. Common IT Security Risk Assessment Template
 circabc.europa.eu
circabc.europa.euIT risks occurring in all sorts of organizations that make use of any type of information and technology. Generally, these risks differ from company to company. However, if you want to assess the common security risks, then you can make use of this Common IT Security Risk Assessment Template. With this PDF template, you can easily assess the IT risks of your company.
5. Corporate Security Risk Assessment
 ntrs.nasa.gov
ntrs.nasa.govCorporate security refers to the process of taking steps or measures to ensure the safety and security of all the assets of the company. These include the employees, IT assets, physical resources, etc. If you want to assess the risks to the corporate security of your organization, then this sample risk assessment template is the best tool. So click on the download icon now!
6. Recommendation IT Risk Assessment Template
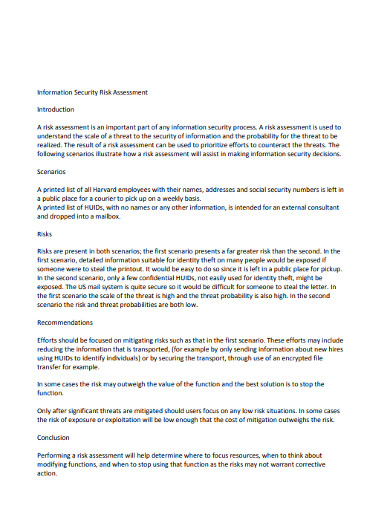 security.harvard.edu
security.harvard.eduConducting risk assessment is a necessary process in all organizations. Not following this step could prove fatal to the company as the risks could later develop into serious problems that are too late to manage. Eliminate this risk for your organization by making a risk assessment for your company with the help of this IT risk assessment template.
7. IT Security Risk Assessment in PDF
 core.ac.uk
core.ac.ukWondering why you need to conduct the security risk assessment for your organization? Well, without this assessment you would not be able to know what is causing problems in your information and technology department. This is why we are offering you this risk assessment template. You can use this assessment sample template to assess your company’s IT risks.
8. Professional IT Security Risk Assessment
 infosecwriters.com
infosecwriters.comCybercrime nowadays is on the rise. And that is why the topic of cybersecurity has become so serious. Wondering how to protect the IT assets of your company? Don’t worry, we can help. With this Professional IT Security Risk Assessment template, you will be able to conduct assessments of your IT risks and ensure the safety of your cyber network.
9. Quantitative IT Security Risk Assessment
 iaeng.org
iaeng.orgIT risk assessment is done in all companies. However, the method followed differs a little. You can use either the quantitative method or the qualitative method. If you are doing the risk assessment using the quantitative method, then you can make use of our security risk assessment template. This template has been specifically designed to help you make such risk assessments.
10. Fundamental IT Security Risk Assessment
 ro.ecu.edu
ro.ecu.eduImagine: you are in a situation where you have tasked with assessing your organization’s security risks. However, you do not how to do it. This is the kind of situation our risk assessment template had been built. Download this template to start making the perfect risk assessments that are suited to the needs of your company.
11. IT Security Self and Risk Assessment Template
 search.org
search.orgWith this IT Security Self and Risk Assessment Template, you can get your hands on a file containing a sample security risk assessment report. This template features original and suggestive headings and content written by professional writers. This template can assist in doing proper IT risk assessments. So what are you waiting for? Download the file now!






