11 Security Risk Assessment Templates – Samples, Examples
In a world with great risks, security is an ever growing necessity. That’s why there is a need for security risk assessments everywhere. The need for formative assessment is impeccable, as you’d want the assessment to have the best results and help you with your fortifications.

It’s normal to protect yourself from possible attacks and security breaches. You may be holding important information that if it falls into the wrong hands, could cost you a lot of losses. Maybe you’d just want to feel secured. Whatever types of assessment you choose, it’s important to know about security risks assessment templates.
Information Security
 assets.kpmg.com
assets.kpmg.comSecurity Threat and Risk Assessment
 cgi-group.co.uk
cgi-group.co.ukRisk Assessment for Physical Security
 onestsolutions.ro
onestsolutions.roSecurity Plan
 worksafe.tas.gov.au
worksafe.tas.gov.auRisk Assessment for HIPAA Security
 nhpco.org
nhpco.orgSecurity Risk Management
 isaca.org
isaca.orgWhat Is the Purpose of a Security Risk Assessment?
Conducting a security risk assessment, even one based on a free assessment template, is a vital process for any business looking to safeguard valuable information. It doesn’t have to necessarily be information as well. It could be an item like an artifact or a person.Whether it’s for physical, or virtual, security, it’s purpose is for:
- Diagnosing possible threats that could cause security breaches.
- Prevent things that could disrupt the operation of an operation, business, or company.
- Provide better input for security assessment templates and other data sheets.
How to Conduct a Security Risk Assessment
Conducting a security risk assessment is a complicated task and requires multiple people working on it. The ones working on it would also need to monitor other things, aside from the assessment. It’s like sending out network assessment templates to everyone individually and personally. Simply put, to conduct this assessment, you need to:
- Have an experienced IT team to check everything.
- They may also need to check the hardware, or the physical aspects of the computer.
- They would also need to update the IT risk assessment templates you have on file, if they find a bug, or a problem.
Risk Assessment for Building Security
 isaca.org
isaca.orgSecurity/Risk Assessment Analyst
 isaca.org
isaca.orgStrategic Security Management
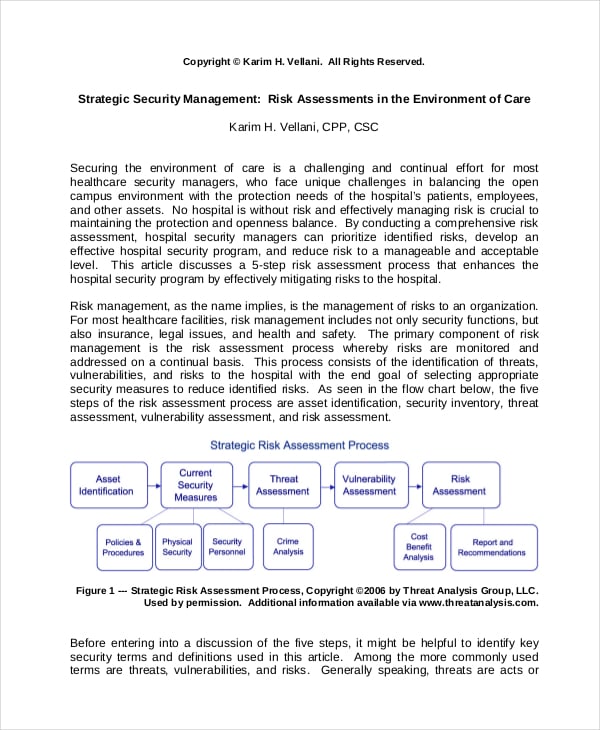 experts.com
experts.comNational Security
 ucl.ac.uk
ucl.ac.ukRisk Assessment for Application Security
 isaca.org
isaca.orgBenefits of Security Risk Assessment
With the process solely focusing on identifying and discovering possible threats, the benefits are definitely amazing. The threat assessment templates your company has would improve as well. Here are some of the benefits it can offer:
- Risk assessment would improve the consistency of your defenses against attacks.
- Since we have improved in terms of technology, there are now security assessments that can operate on their own, saving you time and money.
- Your staff members would now be more aware of the many threats that could possibly endanger everything and not just rely on free assessment templates.
What are the General Steps for a Security Risk Assessment
There are certainly advanced steps when you’re doing security risk assessments. These advanced steps come with complex programming pattern to speed up the process. But if you’re just looking for the simple steps, such as one might find in an assessment template Word, then we have them here:
- Determine the information assets that you are aiming for.
- Locate them and then begin security check.
- Create a threat modeling exercise, as this will let you, and your team practice.
- Save the assessment under the name technology assessment templates, so you can review the results later.






