Table of Contents
- Policy Template Bundle
- FREE 10+ Application Security Policy Templates in PDF | MS Word
- 1. Application Security Policy Template
- 2. Business Support Application Security Policy
- 3. Application Security Executive Policy
- 4. Web Application Security Policy
- 5. City Wide Application Security Policy
- 6. Web Application Security Assessment Policy
- 7. Central Services Web Application Security Policy
- 8. Application Security Policy Example
- 9. Analysis of Web Application Security Policy
- 10. Application Security Policy Governance
- 11. Application Security Policy in DOC
- Steps for developing the Application Security Policy
- FAQ’s
- Why do you need the Application Security Policy?
- How does the Application Security Policy work?
- Do every company must deal with the Application Security Policy?
- What are the actions taken to ensure Application Security?
FREE 10+ Application Security Policy Templates in PDF | MS Word
The Application Security Policy is the management of information security amid new threats. It is the use of the software, hardware, and methods to protect the information from external threats. In software designing, security is becoming an important concern during the development of the application become more frequently accessible over networks and is vulnerable to a wide variety of threats. The ways through which you can safeguard it are policies.

Policy Template Bundle
FREE 10+ Application Security Policy Templates in PDF | MS Word
1. Application Security Policy Template
 nh.gov
nh.gov2. Business Support Application Security Policy
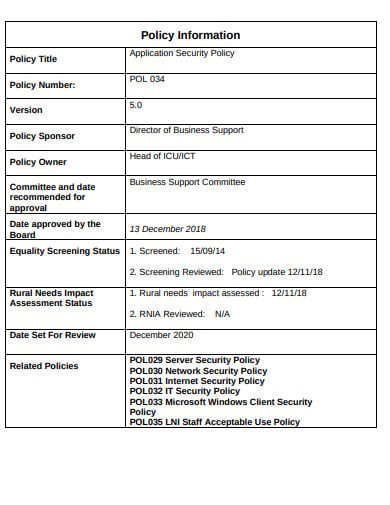 org.uk
org.uk3. Application Security Executive Policy
 in.gov
in.gov4. Web Application Security Policy
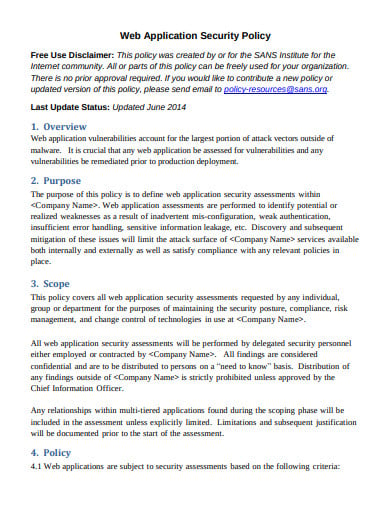 sans.org
sans.org5. City Wide Application Security Policy
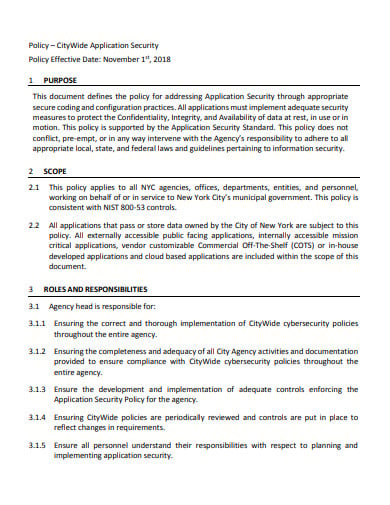 nyc.gov
nyc.gov6. Web Application Security Assessment Policy
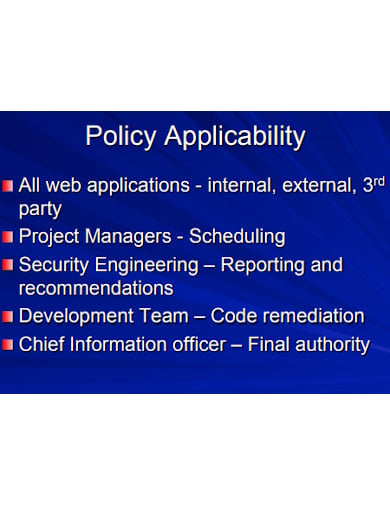 sans.edu
sans.edu7. Central Services Web Application Security Policy
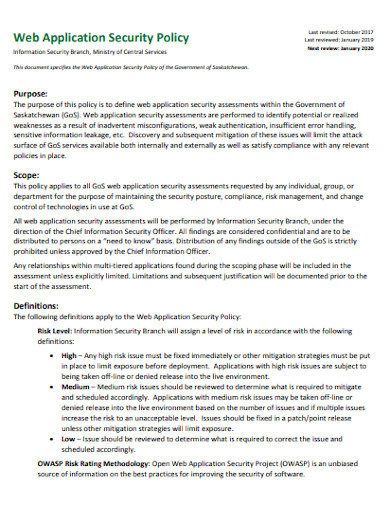 saskatchewan.ca
saskatchewan.ca8. Application Security Policy Example
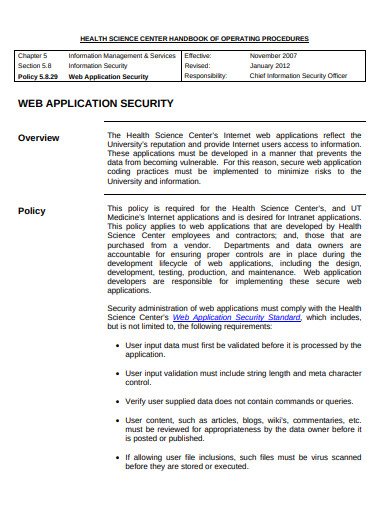 uthscsa.edu
uthscsa.edu9. Analysis of Web Application Security Policy
 berkeley.edu
berkeley.edu10. Application Security Policy Governance
 veracode.com
veracode.com11. Application Security Policy in DOC
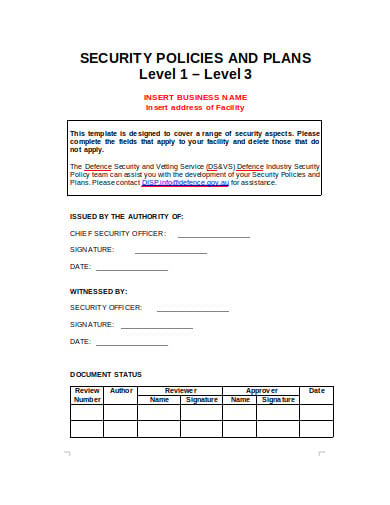 gov.au
gov.auSteps for developing the Application Security Policy
Step 1: Identifying Risk Factors
Is the risk arising from the inappropriate use? Do you have the information that should be restricted? Do you send and receive a huge number of files every day? Do the potentially offensive making the rounds? It can be a non-issue. And this could be costing you a fortune every month in lost employee productivity. The important way to identify the risk factors is the monitoring tool and reporting tools. Many sellers of the firewall and internet security product allow analyzation period for the product.
Step 2: Learn from others
There are many number and types of application security policies, thus it is vital to visualize what alternative organizations like yours do. The risk factors in the web application development and its securities are common among the organizations. It is important that you go through the security policies and the tools that this company owns to avoid the serious circumstances taking place in an organization’s security system. We can take an example from the others who are using these tools.
Step 3: Make sure the policy conform legal needs
Depending on the information holdings, jurisdiction and placement, you will be needed to evolve to sure minimum standards to confirm the protection and integrity of your knowledge, particularly if your company holds personal information. Having a viable security policy documented and in place is the one technique of mitigating any liabilities you might incur in the event of a security breach.
Step 4: Measuring the level of risks
Don’t be overzealous.. An excessive amount of privacy are often as dangerous as insufficient. You would possibly decide that, excluding keeping the dangerous guys out, you do not have any problems with applicable use as a result of you have got a mature, dedicated workers. In such cases, a written code of conduct is that the most vital issue. Excessive security are often a hindrance to swish business operations, therefore confirm you do not overprotect yourself.
Step 5: Installing tools that you require
Having the policy is one thing, enforcing it is another. Internet and e-mail content security products with customizable guidelines sets can ensure that your policy, no matter how complex, is adhered to. The investment in tools to enforce your security policy is definitely one of the most cost-effective purchases you will ever make.
FAQ’s
Why do you need the Application Security Policy?
The safety measures in the form of the policies built into the application and the sound application security routine minimize the likelihood that unauthorized code that will be able to manipulate the application to access, steal, modify, or delete the sensitive data. The activities to ensure application security or sometimes are called safety measures. There is a common software application installed to stop operating the system through the use of it.
How does the Application Security Policy work?
The Application Security Policy is the measures that take care of the protection of the information system. The most safety measure is the application firewall that limits the execution of the files or the handling of the data by the specific installed programs. The most common safety measure is the router that can prevent the IP address of the individual from being directly visible on the internet. The implementation of the application security policies is an important step.
Do every company must deal with the Application Security Policy?
It is necessary that it should spent some part of the revenue in the safety measures of the organization as it is considered as one of the basic elements when you run an organization. The protection measures are important for the organization to function smoothly as there are the miscreants that shall want to invade the privacy of the company. And for this purpose, the need for a strong policy is important for the safety and security of the application.
What are the actions taken to ensure Application Security?
There are countermeasures that ensure the safety of the application and software includes the conventional firewalls, encryption/decryption program, anti-virus programs, spyware detection removable programs, bio-metric authentication programs, etc. The application security shall be enhanced by defining the enterprise’s assets, identifying what does each of the applications does with respect to these assets, creating the security profile for each application.






