Table of Contents
- Policy Template Bundle
- FREE 11+ System Policy Templates in PDF | MS Word
- 1. Control and System Policy
- 2. Integrated Management System Policy
- 3. Management System Policy
- 4. IT System Maintenance Policy
- 4. Learning Management System Policy
- 5. Quality System Management Policy
- 6. Information System Management Policy
- 7. Environmental Management System Policy
- 8. HR Management System Policy
- 9. Player Points System Policy
- 10. Intend System Policy
- 11. System Level Security Policy
- 12. Service Delivery System Policy
- 5 Steps to develop the system policy
- FAQ’s
- Why do you need the System Policy?
- How does the System Policy work?
- What is the advantage of the System Policy?
- Why is the system policy considered to be important to the enterprise?
FREE 11+ System Policy Templates in PDF | MS Word
The System policy is the security policy that frequently does not look like other types of policy. They may function as standards or the procedures to be used when configuring or maintaining the systems. These policies can be separated into management guidance, technical specifications or combined in a single policy document. Each system has own underlined policies. The system policy is for the user to understand the risks they can cause the organization by exposing them to things.

Policy Template Bundle
FREE 11+ System Policy Templates in PDF | MS Word
1. Control and System Policy
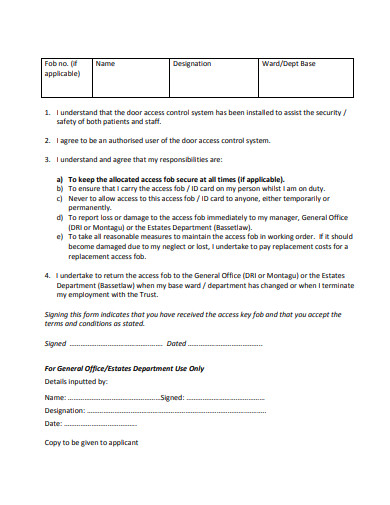 nhs.uk
nhs.uk2. Integrated Management System Policy
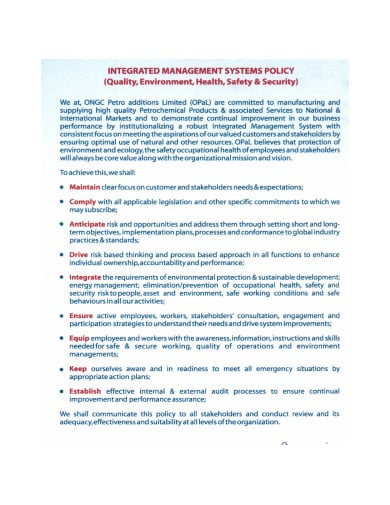 opalindia.in
opalindia.in3. Management System Policy
 group.com
group.com4. IT System Maintenance Policy
 nc.gov
nc.gov4. Learning Management System Policy
 edu.au
edu.au5. Quality System Management Policy
 materials.com
materials.com6. Information System Management Policy
 ac.uk
ac.uk7. Environmental Management System Policy
 auburn.edu
auburn.edu8. HR Management System Policy
 csun.edu
csun.edu9. Player Points System Policy
 com.au
com.au10. Intend System Policy
 angliauk.com
angliauk.com11. System Level Security Policy
 hscic.gov
hscic.gov12. Service Delivery System Policy
 wa.gov
wa.gov5 Steps to develop the system policy
Step 1: Create the policy in Word Document
The policy document can be created in the word application as it is easy and simple to make it using the software. The construction of the policy is important on the part of the safety and security of the organization. The policy have to be simple and editable as you can keep on checking from time to time and make changes on it when required. The policy maker should negotiate among the other members in the management for the implementation of it.
Step 2: Construct the structure
After planning to create the policy, it is significant to decide the structure that you want to give to the policy for a better outlook and effective. The structure of the policy highly depends on the success of it in eradicating the issues and problems in the organization. So, while constructing the structure, it is important that you have a clear idea of its implication.
Step 3: Include the important inputs
The policy must include the important and the significant input in it as it will be eradicating the security issues in the organization’s technical system. And for this purpose, you need to have the advice of the experts who has sheer experiences in the technical field. There should be continuous changes in the policy with the need and requirement.
Step 4: Revise the policies
The revision of the system policies is the most required thing while you plan it to implement in the organization. The evaluation and review of the policies from time to time will lead you to the deduction in the error in the process. With the review, the policies will be developed with the arising situation.
Step 5: Implement it
The implementation of the policies in the organization shall be the final stage of the process. Therefore, the objective of the policies shall be met with the proper evaluation and analysis from the members in the management. The continuous observation and analysis will keep pace with the upcoming situations that threaten the privacy and security of the organization.
FAQ’s
Why do you need the System Policy?
It is the quiet common practice to require new employees to sign an acknowledgment before receiving any access information. It must be done with the time intervals or whenever significant changes occurred to the environment. The System Policy must stay adequate and effective under the current state of the organization’s information security department. There must be opportunities for further improvement of the security posts to avoid intrusion by the external forces.
How does the System Policy work?
The basis of these policies was defined, which is hopefully only from the risk management process like the contents of the policy, any exceptions to the policies including why, the policy approval process, how the policy has been implemented, the employee awareness training, an audit of the review or update process, etc. The policy is generally the blueprint to do the things in the process and what will be the further goals and objectives of implementing the policies.
What is the advantage of the System Policy?
The system policies are more dynamic and may subject to the changes and therefore they should be reviewed more often. It should be written clearly, concisely, so they can easily understand and follow it. The steps should be created by the process owners and reflect the translation of the security policies. The policies are reviewed to evaluate the effectiveness of the process. The policies are documented, understood and implemented, etc. The policies guarantee success if reviewed and transparent in nature.
Why is the system policy considered to be important to the enterprise?
The situation where you might face the security issues in the enterprise like intervention by the stranger, some unidentified calls, leaving the logged-in system with someone, taking the company equipment back to the home, etc. These are some of the common situations arise in every workplace and these can be avoided when you have the system security policy to manage. The need for the system policy by the enterprise is an important step to take.






