Table of Contents
- Policy Template Bundle
- 5 Steps to Prepare Security Assessment and Authorization Policy
- 7+ Security Assessment and Authorization Policy Templates in PDF
- 1. Information Security Assessment and Authorization Policy
- 2. Business Security Assessment and Authorization Policy
- 3. Security Assessment and Authorization Policy Template
- 4. Security Assessment and Authorization Policy Example
- 5. Security Assessment and Authorization Policy Template
- 6. Security Assessment and Authorization Policy in PDF
- 7. Standard Security Assessment and Authorization Policy
- 8. Basic Security Assessment and Authorization Policy
7+ Security Assessment and Authorization Policy Templates in PDF
A security assessment and authorization policy is the system where the security risk is assessed and a risk management policy is developed as an authorization policy. The security assessment is done to analyze and evaluate the risk, and authorization is the implementation of policies that can prevent the risk from taking place. Here are some policy templates that can help you formulate the security assessment and authorization policy.

Policy Template Bundle
5 Steps to Prepare Security Assessment and Authorization Policy
Step 1: Draft the Document
Draft the document where you write about all the important information. You can use the MS Word as a computer application. This software is the simplest software available. You can use it on both Windows and iOS. When you open the Word file you will get the blank page. Choose the type of font you want to use the style and the size, the structures you want to give to the whole document, etc.
Step 2: Scope of the Assessment
The scope is an essential element of the assessment process. Without knowing the scope, you can not proceed further with the assessment. You need to understand the direction your assessment is going and what will be the outcome of the assessment. You need to be aware of the opportunities and the possibilities that you will encounter with the assessment.
Step 3: Purpose of the Assessment
The main purpose of the assessment is to find out the security issues or the problems associated with security. Your goal is to find out those problems and assess them so that you can come up with policies that can help you to prevent them or reduce the frequency of the possible impact.
Step 4: Find the Issue
This step involves the search for the issue. Assess thoroughly so that you can do the in-depth analysis and find out all the problems. After finding out the problem, only then you will be able to assess the magnitude of the security-related problem.
Step 5: Design the Authorization Policy
Now that you have done the assessment, it is time to formulate the authorization policy. Design the policies that will be impactful and helpful, for preventing any security-related problem. Follow these policies so that you can reduce any kind of adverse effect or problem.
7+ Security Assessment and Authorization Policy Templates in PDF
1. Information Security Assessment and Authorization Policy
 maricopa.gov
maricopa.govIn case you want to develop a proper information security assessment and authorization policy for the organization to avoid any damage to the database, download this Information Security Assessment and Authorization Policy. This policy template in PDF comes with detailed information. You can use this information to prepare the policy that you think is suitable for your company.
2. Business Security Assessment and Authorization Policy
 policy.tennessee.edu
policy.tennessee.eduIf you are running a business you have the responsibility to look after the security measures. Download this Business Security Assessment and Authorization Policy template so that you can device out a plan where you can analyze the risks related to your business and develop the measures to combat them. This security policy template is instantly downloadable. You can also edit it in the PDF editor for any required changes.
3. Security Assessment and Authorization Policy Template
 uttyler.edu
uttyler.eduIn case you want to draft the report regarding the security issues, the assessment, and the authorization policies, check out this Security Assessment and Authorization Policy Template. This assessment template is modifiable in nature. That means you have the authority to customize the provided content and input your required content in the structure.
4. Security Assessment and Authorization Policy Example
 michigan.gov
michigan.govDo you want to design a summary of the security risk assessment and the IT policy developed after that? Then download this Security Assessment and Authorization Policy Example template. If you download this template you will get the information that you can use as the referential element for the summary you are going to write. The content that is mentioned in the template is for the benefit of the customers who will be developing the policies.
5. Security Assessment and Authorization Policy Template
 forcepoint.com
forcepoint.comMake all the new employees familiar with the acronym for the assessments and the authorization. Download this Security Assessment and Authorization Policy Template and use this as the base structure for your important document. You can use the data provided in the template as well as make your desired additions and subtractions. The moment you download this privacy policy template it is your responsibility how you want to use it.
6. Security Assessment and Authorization Policy in PDF
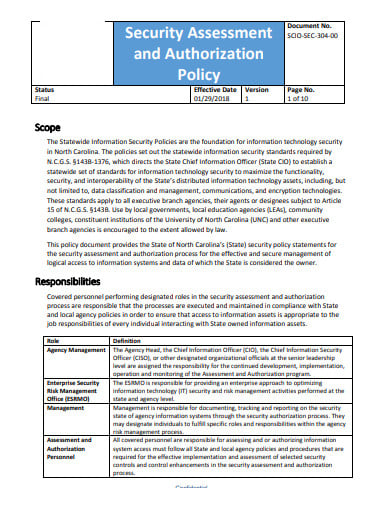 files.nc.gov
files.nc.govExplain the scope, responsibilities, roles, etc. that are required and are a very important part of security assessment and authorization policy. Download this Security Assessment and Authorization Policy in PDF template, so that you can prepare a proper assessment report, which will help your organization to handle the issues related to securities. You may use this template as an example to support your report.
7. Standard Security Assessment and Authorization Policy
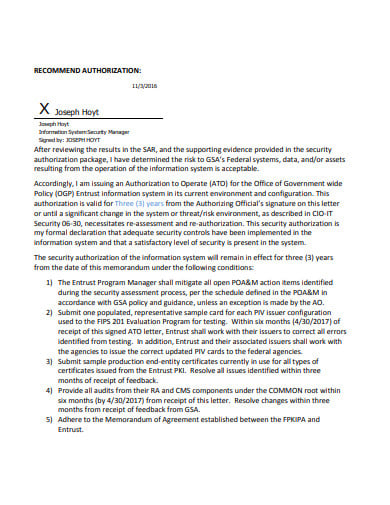 idmanagement.gov
idmanagement.govThis Standard Security Assessment and Authorization Policy template have been crafted so that we can provide our customers with a ready-made structure and some information that can speed up their process of preparing the record of all the assessment related material and the policies that are authorized to be followed after the assessment. This security assessment template is prepared with instructions that can guide you to work on your policy.
8. Basic Security Assessment and Authorization Policy
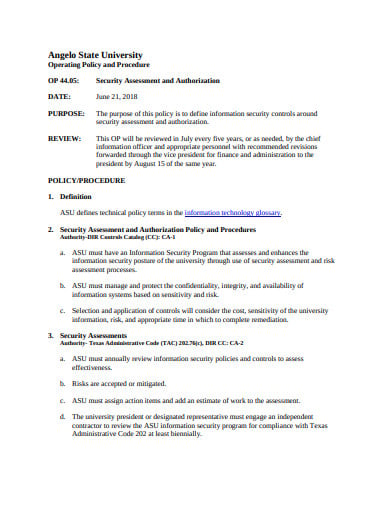 angelo.edu
angelo.eduAs an organization, if you want to make a list of basic rules and regulations that you want to follow related to the security issues, you can avail of this Basic Security Assessment and Authorization Policy template. In this template, you can get the idea and sample of basic steps that you can execute to develop your list. This PDF template can be modified as per your preference. You can make all the required changes that you need.






