Table of Contents
- Checklist Template Bundle
- FREE 10+ Application Security Checklist Templates in PDF | MS Word
- 1. Application Security Checklist Template
- 2. Third Party Application Security Checklist Format
- 3. Client Application Security Checklist Template
- 4. Mobile Application Security Checklist in PDF
- 5. Web Application Security Checklist Template
- 6. Application Security Checklist Example
- 7. Application Security Testing Checklist Template
- 8. Basic Application Security Coding Checklist
- 9. Consultants Application Security Checklist Template
- 10. Standard Application System Security Checklist
- 11. Operating System Application Security Checklist Template
- 5 Steps to develop the Application Security Checklist
- FAQ’s
- How does the Application Security Checklist work?
- What are the uses of the Application Security Checklists?
- Why do you need the Application Security Checklists?
- What is the effect of using the Application Security Checklists?
FREE 10+ Application Security Checklist Templates in PDF | MS Word
The Application Security Checklist is the process of protecting the software and online services against the different security threats that exploit the vulnerability in an application’s code. Common targets for the application are the content management system, database administration tools, and SaaS applications. The organizations failing to secure their applications run the risks of being attacked.

Checklist Template Bundle
FREE 10+ Application Security Checklist Templates in PDF | MS Word
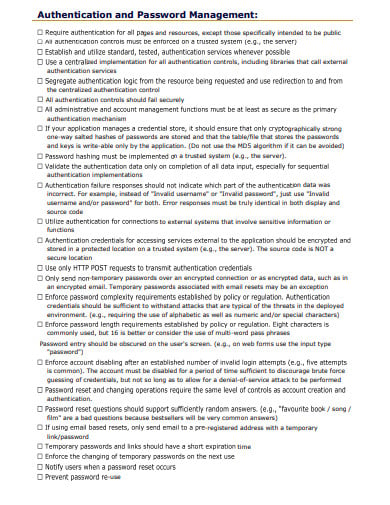
1. Application Security Checklist Template
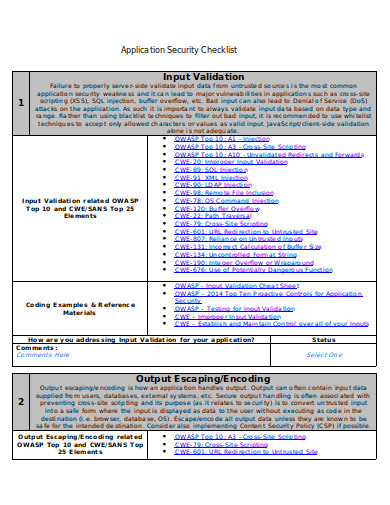 uci.edu
uci.edu2. Third Party Application Security Checklist Format
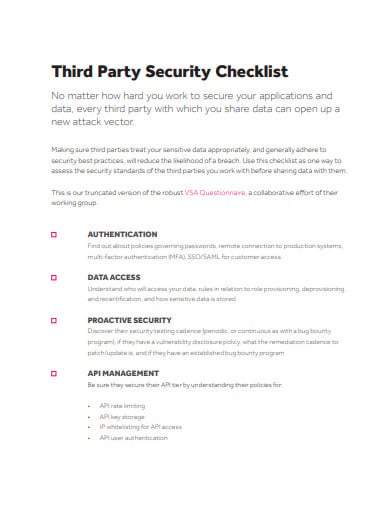 hackerone.com
hackerone.com3. Client Application Security Checklist Template
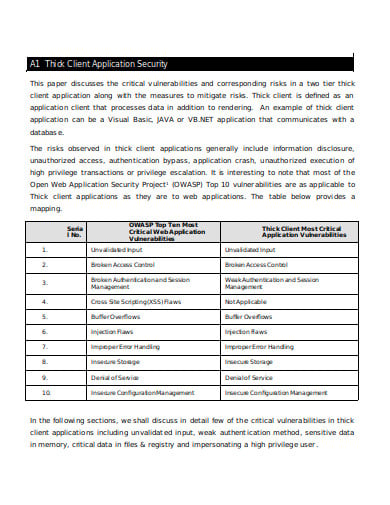 owasp.org
owasp.org4. Mobile Application Security Checklist in PDF
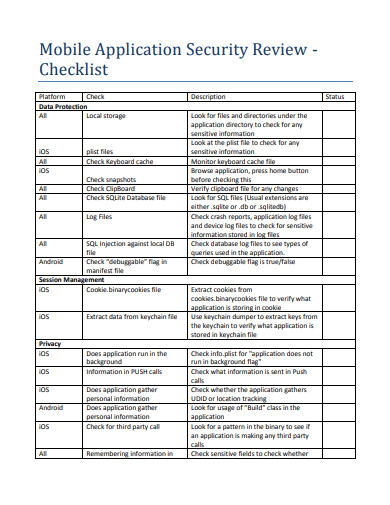 blueinfy.com
blueinfy.com5. Web Application Security Checklist Template
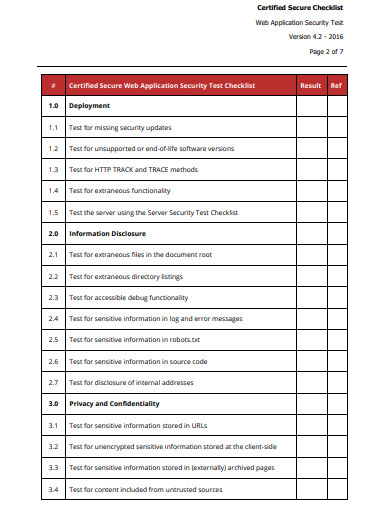 certifiedsecure.com
certifiedsecure.com6. Application Security Checklist Example
 paper.seebug.org
paper.seebug.org7. Application Security Testing Checklist Template
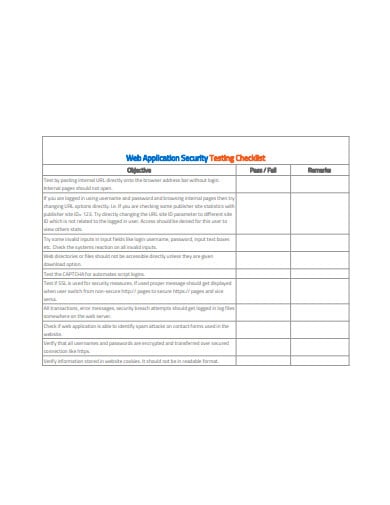 ravedigital.agency
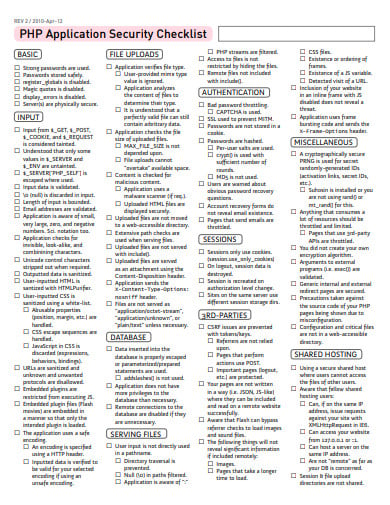
ravedigital.agency8. Basic Application Security Coding Checklist
 testandverification.com
testandverification.com9. Consultants Application Security Checklist Template
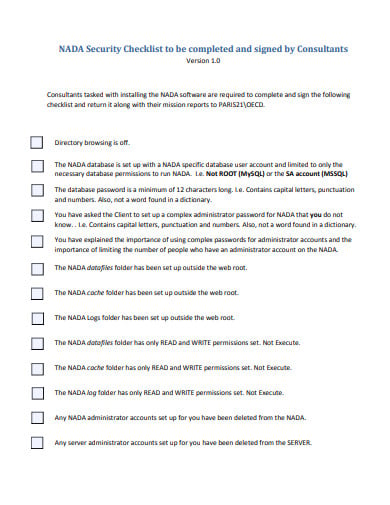 ihsn.org
ihsn.org10. Standard Application System Security Checklist
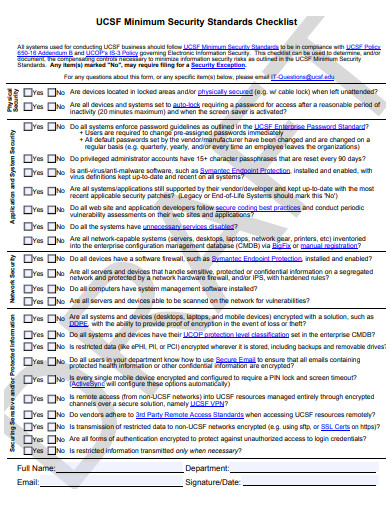 it.ucsf.edu
it.ucsf.edu11. Operating System Application Security Checklist Template
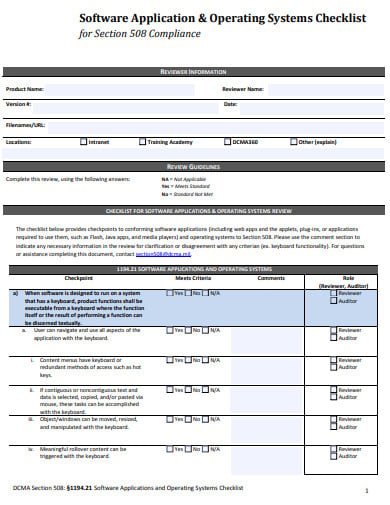 dcma.mil
dcma.mil5 Steps to develop the Application Security Checklist
Step 1: Putting the Right Tools
The selection of the right tool is really important when you prepare the checklists for the application security purpose. The use of the checklist in the organization is the first thing that you make while preparing for the security and the safety measures in it. The usage of the checklist is significant in this process as team follows the process and methods in it to provide the security from the risks factors.
Step 2: Pick team with Enough skills and resources
When you plan the application security, you need an efficient team that will, later on, conduct the plan and makes it successful by bringing it to the expected conclusion. And for this, you have to make the team of the skillful and efficient people that can figure out ways through which you can easily make the entire process successful.
Step 3: The Area need to be tested
The scope of the security checklist must be really important. And you need to get all the right people on the board. It must be clear that which network system, applications that you have to test, the way you will test them, and what are the deliverable expectation from this.
Step 4: Select the tools for the tasks
For authenticated testing, you need the tools that allow you to attempt to manipulate the user logins, session management, application workflows and so on. But unfortunately, most of these tools are pricey, as it is required and important. It should be done every now and then.
Step 5: Vulnerability Scanning
Rather than trying to create the checklists of every test that you need to run for every vulnerability for application security testing. Then it becomes easier to break it down into the different categories. When running the vulnerability scans, make sure the scanners are testing for the big things. The careful handling of every tool and system is the core responsibility of the experts.
FAQ’s
How does the Application Security Checklist work?
The Application Security Checklist includes the solutions and the enforced security procedures should be deployed to avoid such threats. There are application firewalls are hardware and the software solutions used for the protection from application security. These Solutions are designed to examine the incoming traffics to block the attack attempts, thereby compensating for any kind of code sanitation deficiency. By securing data from theft and the manipulation, it creates the safety wall for the organization.
What are the uses of the Application Security Checklists?
There is a number of methods for securing the applications. And it is the part of any application security checklist. The gathering of the information by manually reviewing the application, identifying the entry points, client-side codes, classifying the third-party hosted content. Testing the application for the path traversals, the vertical and horizontal access control issues, missing authorization and insecure, direct object references, etc. Securing the data transmissions.
Why do you need the Application Security Checklists?
Application Security is the crowded confusing field. And it grows more confusing every day as the cyber threats increases and new application security enters the market. Securing the applications against today’s cyber threats means facing the various jungle of the products, services, and solutions. The security checklists outline that describes how to secure your applications and protect your data in the current threat environment. The elimination of the vulnerabilities before it goes to production.
What is the effect of using the Application Security Checklists?
As we know that every application becomes vulnerable when they are exposed to the internet. There are a number of the best practices and the countermeasures that developers can use when they build their applications. Most of the firewalls reside behind perimeter firewalls, routers, and various types of filtering devices. Always make sure that the devices use the filtering traffic are stateful packet inspection devices. Blocking the unnecessary types of traffics to support the applications.






