Table of Contents
- Checklist Template Bundle
- FREE 4+ Desktop Security Checklist Templates in PDF
- 1. Free Desktop Security Checklist Template
- 2. Free Desktop and Portable Computer Security Checklist
- 3. Free Personal Computer Security Checklist
- 4. Free Computer Security Checklist Template
- 5 Steps to develop the Desktop Security Checklist?
- FAQ’s
- Why do you need the Desktop Security Checklist?
- What is the purpose of the Desktop Security Checklist?
- How does the Desktop Security Checklist work?
- What is the pre-production Desktop Security Checklist?
FREE 4+ Desktop Security Checklist Templates in PDF
The Desktop Security listing consists of substantiating the security of computer settings to work out if they’re set fitly and in keeping with the knowledge security policy.. It is needed by all the workstations and organizations. The objective of creating the desktop security checklist is to provide maximum security to the desktop system of the company. This sample checklist is designed to improve system privacy and security. This will check things off to keep track as you go.

Checklist Template Bundle
FREE 4+ Desktop Security Checklist Templates in PDF
1. Free Desktop Security Checklist Template
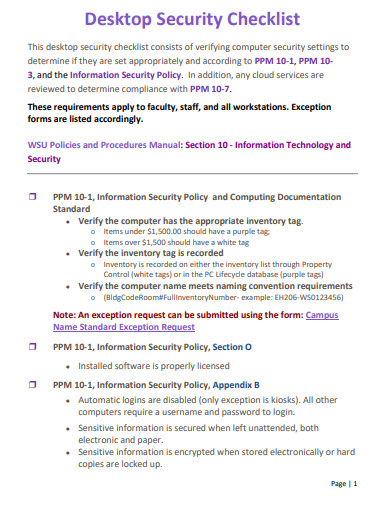 weber.edu
weber.edu2. Free Desktop and Portable Computer Security Checklist
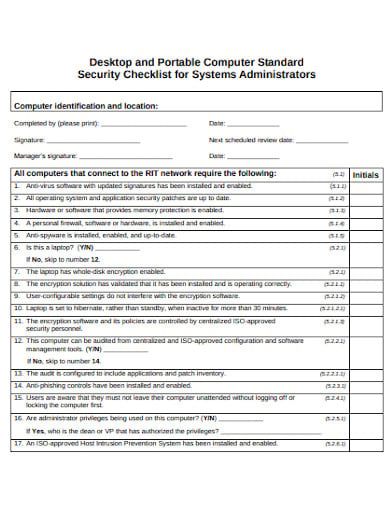 rit.edu
rit.edu3. Free Personal Computer Security Checklist
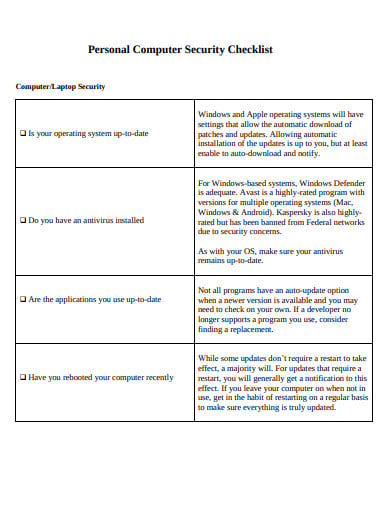 wi.gov
wi.gov4. Free Computer Security Checklist Template
 dvbat5idxh7ib.cloudfront.net
dvbat5idxh7ib.cloudfront.net5 Steps to develop the Desktop Security Checklist?
The desktop security checklist is the list of the security measures that you must implement to protect the system from infiltrates. It is a vast and fast-moving topic. And not a single rule can cover all the possible situations. Hence the simple checklist is for catching all the common doubts and problems that you might have when considering the process of system security. Here are the steps discussing some of the ways to build the desktop security checklists
Step 1: Prepare the Word Document
Firstly, open the word document and prepare the checklist on it. With the use of the word document, you can make preferable changes in the font size and plenty of things. Like you can edit the entire document when you have to make changes in it. You can use different layouts, colors, in the document which will make the document look quite attractive. The document can be saved in the system and used whenever necessary. The word document is effective in making a modern checklist.
Step 2: Form the Structure
When you decide to make the checklist in the word document. It is important that you think of the particular structure to shape your document. It has been quite simple and easily understandable so that people can easily get the things mentioned in it. Following the structure of the creative checklist, one can build the efficient and useful checklist for desktop security and protection.
Step 3: Mention inputs in it
Then, here you need to put the inputs and the things that you were thinking to put in the basic checklist. The things are important mentioning in the checklist like the guidelines and the policies for the safety measures. The ways and the methods through which you can stop the infiltration of the organization’s technical system. With the proper inputs in the professional checklists, you can develop the measures and policies for the organization.
Step 4: Revision of document
At the end of the process of creating the quality checklist, it is important that you go through the checklist and make changes in it if needed. You can make an evaluation of the process by discussing the content of the checklists with the other members of the organization. And with the consent, you can take this layout checklist to the next phase of the execution.
Step 5: Execution
With the completion of the evaluation process, the checklist is ready to be executed and bring to the action to secure the organization’s technical system. The checklist is the tool through which you can bring drastic changes in the technical department by securing the system in a more systematic manner. You can also see more on Desktop Templates.
FAQ’s
Why do you need the Desktop Security Checklist?
The desktop security checklist is a useful and essential tool for the governance, control, safeguard of the system of an organization. The main aim of the format checklist is to cover a wide range of areas that are crucial to the organization’s IT security. The checklist should help the IT team design and execute effective safety measures for the organization. For a better understanding, it must be simple and sophisticated in nature. This is the must-have thing before planning to make a checklist. You can also see more on Security Templates.
What is the purpose of the Desktop Security Checklist?
The checklists can be designed by adding more nuances and details that suit your organizational structure or practices. The basic design consists of the various areas and sections like the risks of the current status, the planned action or area of improvement. Hence, it becomes essential to have a comprehensive and clearly articulated policy in place that can make the organizations member understand the importance of privacy and protection.
How does the Desktop Security Checklist work?
It is not possible to expect your organization to secure itself without having the correct resources and the dedicated set of people working for it. When there is no proper structure in the place and responsibilities are not clearly defined, then there are the high risks of the breach of the rule. Therefore, it is essential to have a useful tool to manage security and privacy, it can be fulfilled by preparing the proper checklist for your organization. You can also see more on Hr Checklist.
What is the pre-production Desktop Security Checklist?
There is the pre-production desktop security checklist like enabling access control and enforcing authentication, configuring the role-based access control, encrypting the communication, encrypt and protect the data, limit system exposure, audit the system activity, etc. So, these are some of the measures that you can include in the checklist to protect the system from getting corrupted by the external forces. The organization has to prepare the checklist to safeguard the important content from getting misused by infiltrates. You can also see more on Training Checklist Templates.






