15+ Network Penetration Testing
A pen test, short for a network penetration test, is a test that is conducted to ensure that a software, a computer, or a network is free from security blunders that a malicious software such as a Trojan or a virus can get in through. Like most users, most website owners need to worry about whether or not their website offers a safe browsing experience to its customers. You can also see Cloud Based Testing Tools.
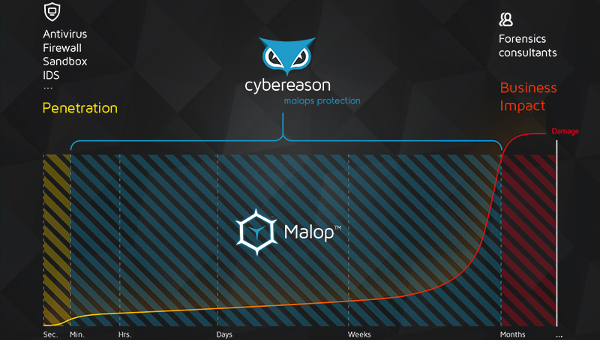
This is precisely why pen tests tools gain in popularity to this extent. The test tool points out areas in a network that are not protected and can be exploited by viruses or can be used as a medium for phishing and other unfair internet activities. See this Responsive Testing Tools.
Veracode Penetration Testing Tool
Veracode Penetration testing tools are used as a test to automate tasks and improve testing efficiency. It also discovers the problems which is difficult to find using manual analysis techniques.There are two types of penetration testing tools, one is static analysis tools and another one is dynamic analysis tools. Veracode performs both and solves the security issues which might harm the system.
Cigital Network Penetration Testing Tool
Cigital network penetration testing detects the problem networks which are vulnerable. They solve the issues and they reduce the breach which might happen. There network searches in all the delicated areas from which damage may happen and they solve the issues with utmost grace.
Network Penetration Testing Rhino Security Tool
Rhino Security Labs tests beyond simple vulnerability scans and provide much impactful security analysis. This way it allows flexibility to clients scope and technology. It employs industry top experts to give the best services to you. They run their test on web mobile apps, virtualized environments, cloud and hybrid architectures, SCADA etc.
Akamai Network Penetration Testing Tool
Akamai Network Penetration Testing Tool secures data and website from the threat. It also reduces the risk of data theft and downtime. It protects the larger attacks and safeguards the website from the vulnerable areas. It performs all the services without any effect on performance.
Redspin Professional Penetration Testing
Redspin has got world class penetration testing security engineers. They deliver the best of services which ultimately lowers the risk by securing them against any vulnerabilities which might slips through or be able to escape advanced analysis. They have an expertise team to solve the issues.
Infrastructure (Network) Penetration Test Tool
Infrastructure (Network) Penetration Test Tool Identify the network’s issues and vulnerabilities even before the threats. It gives a solution for testing IT network infrastructure and ensuring that your organisation is secured against cyber threats and related issues it fixes the vulnerable areas quick and fast.
ControlScan Network & Application Layer Penetration Testing
It is trusted by more than 1.1 million companies around the globe. It has got a strong hold on managed security and compliance services. This has a notion that Data security is a serious business that is why it should be ahead of the threats. It continually upgrades so that you can focus on building your business. It is a wall of protection in your network, data, applications and devices.
Clone-Systems Penetration Testing Service
Clone-Systems Penetration Testing Service is an award winning service. It supplies penetration testing services to large enterprises and small businesses. It gives deep insight into the threats. It is designed for compliance regulations such as PCI, FDIC, HIPAA, GLBA, Sarbanes-Oxley, NCLUA and others. They provide solution to the threats and risks present in today’s technological environments. It identifies all vulnerabilities within the infrastructure and provide recommendations and improvements to keep the business safe and protected.
HackLabs: Penetration Testing & Web Application Security
Penetration Testing & Web Application Security examines internal IT systems for any weakness that could be used to disrupt the confidentiality and it allows to solve the weakness.it has got ways to solve problems in thr araes like internal network scanning, port scanning system, fingerprinting Services etc.
Security Assessment – Wireless Penetration Testing
Security Assessment – Wireless Penetration Testing an approach to conduct a mix of black and white box testing. It initiates through a site survey and locate access points. They identify and detect vulnerabilities within the wireless spectrum and proceed with a white box test component.
Nettitude Website Penetration Testing Tool

Nettitude Website Penetration Testing Tool is a global provider of penetration testing services.It does cyber security testing, security auditing and PCI services. They deliver engagements which shows the vulnerabilities in infrastructure, application, mobile devices and wireless.






