Bring Your Security Plans to Life with Security Roadmap Templates from Template.net
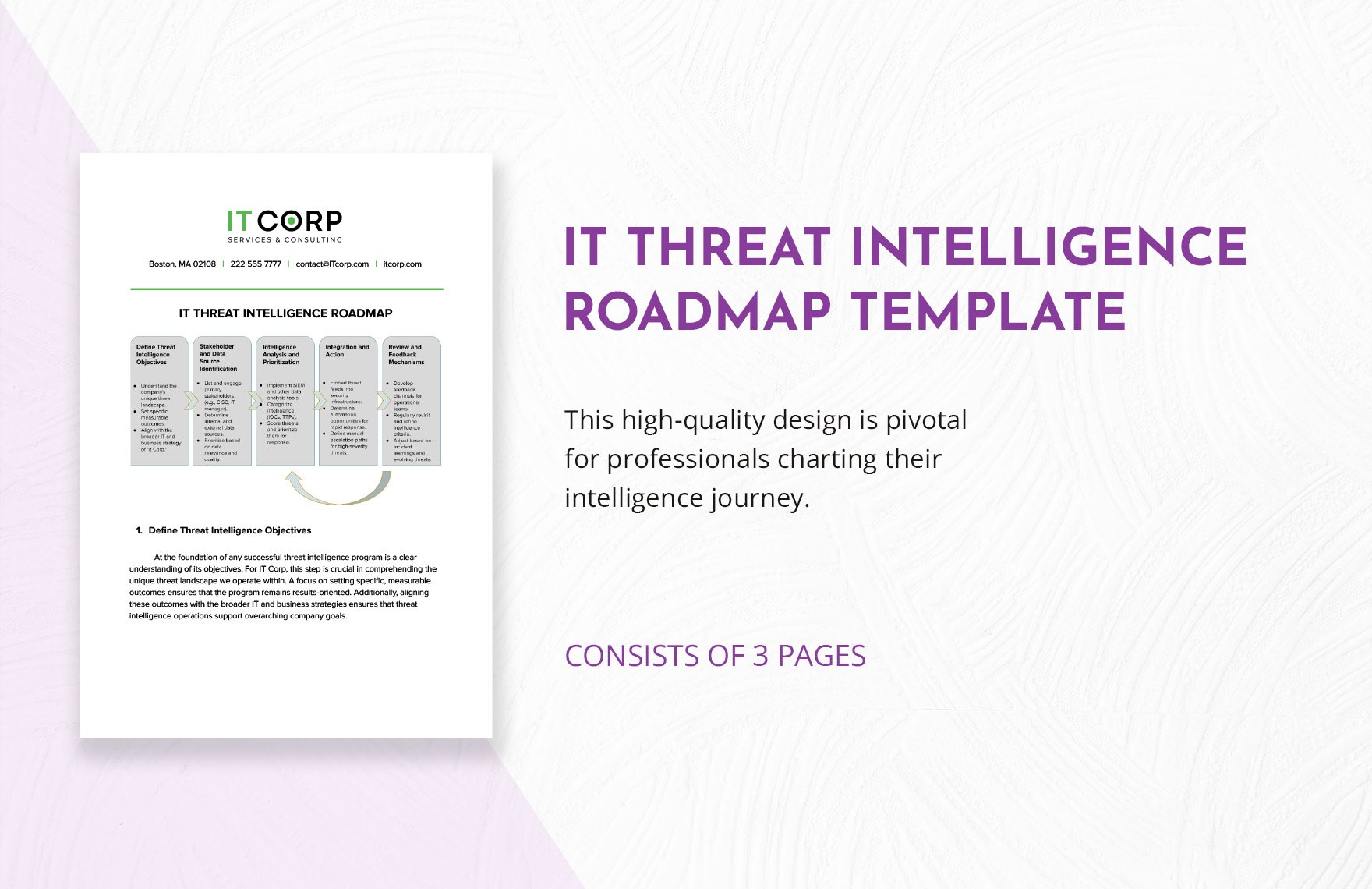
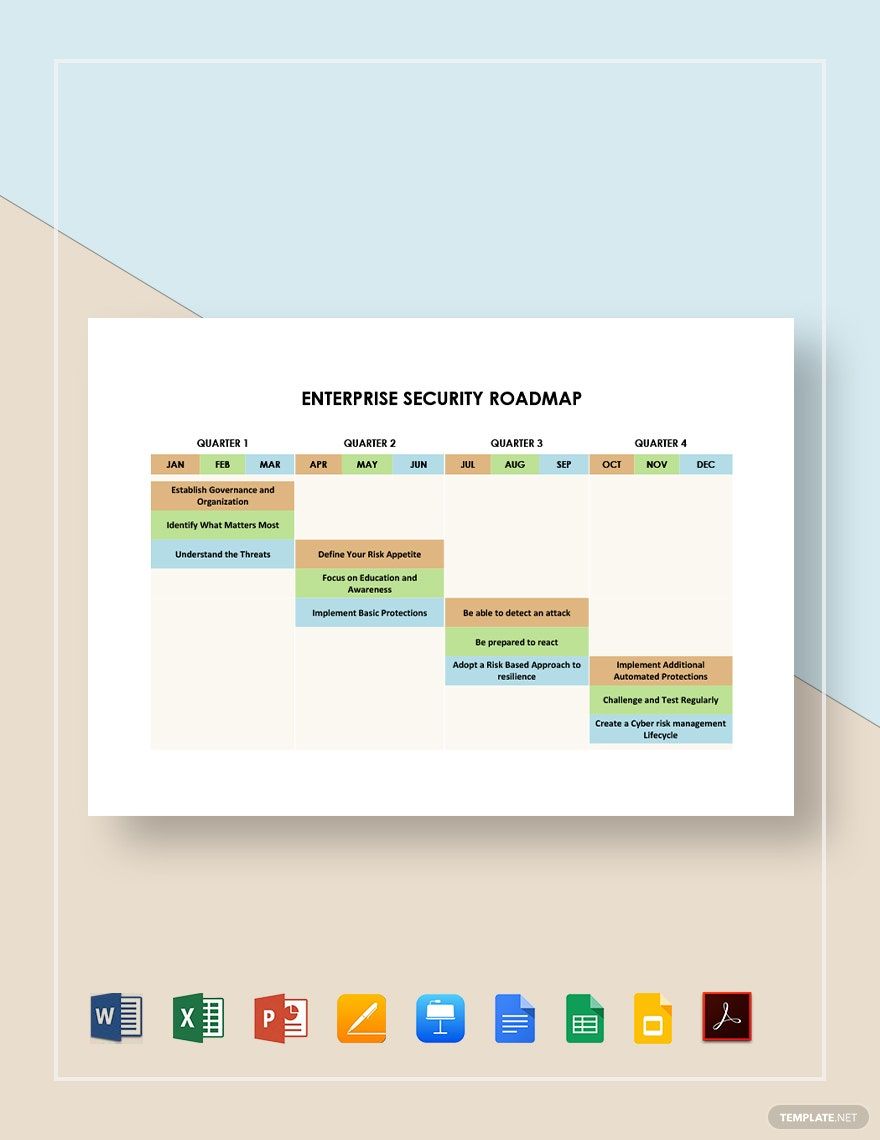
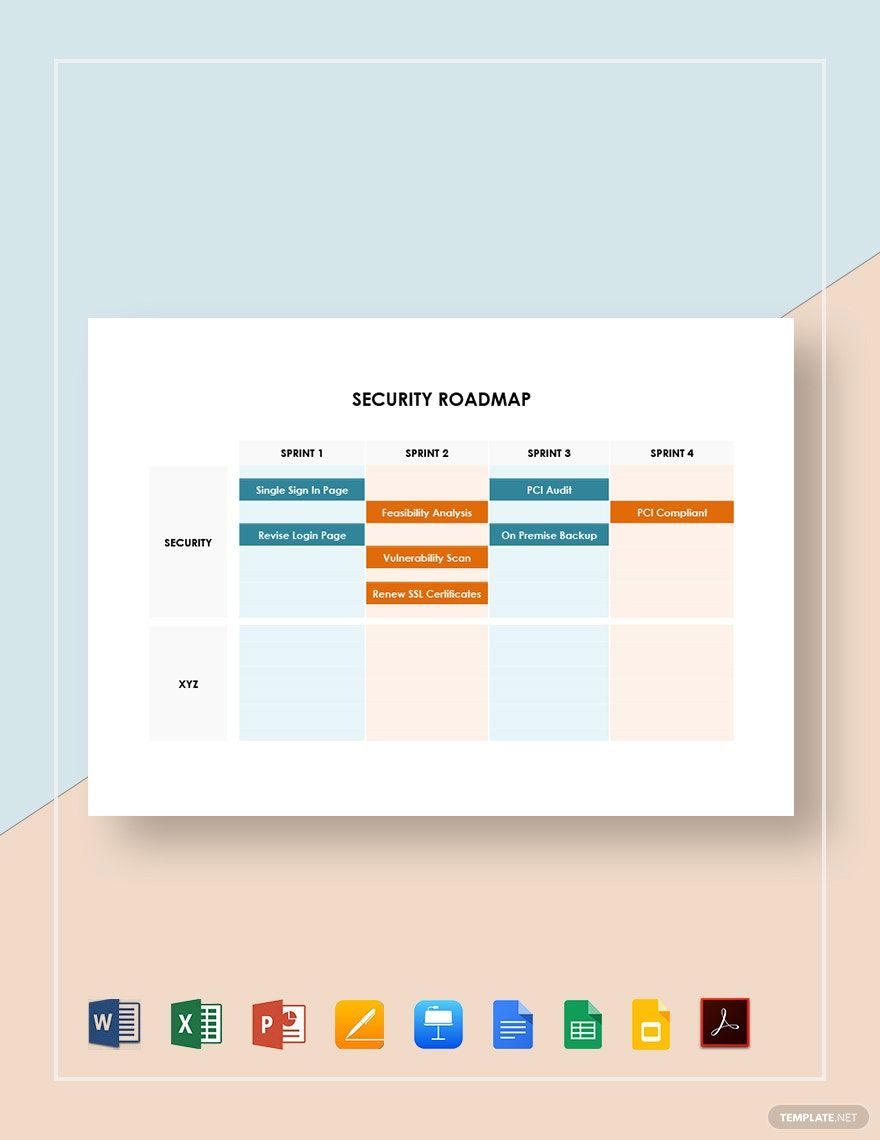
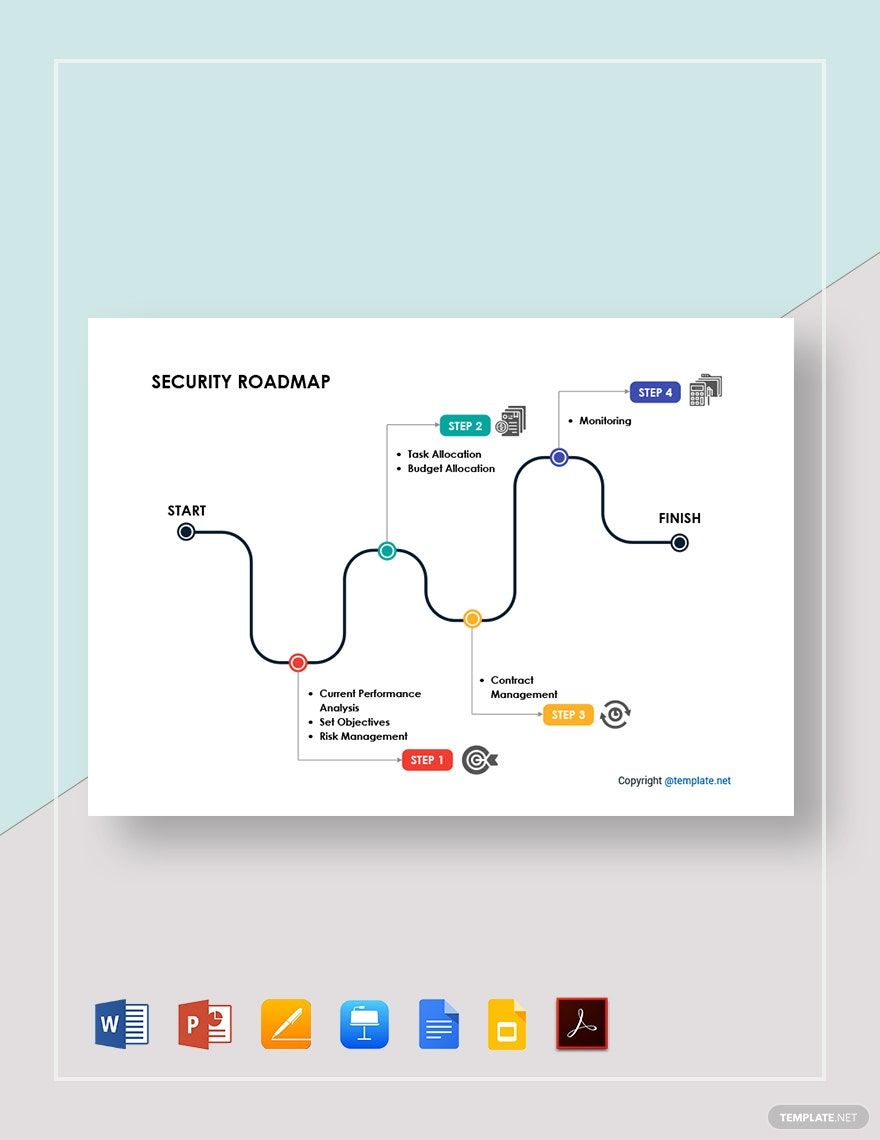
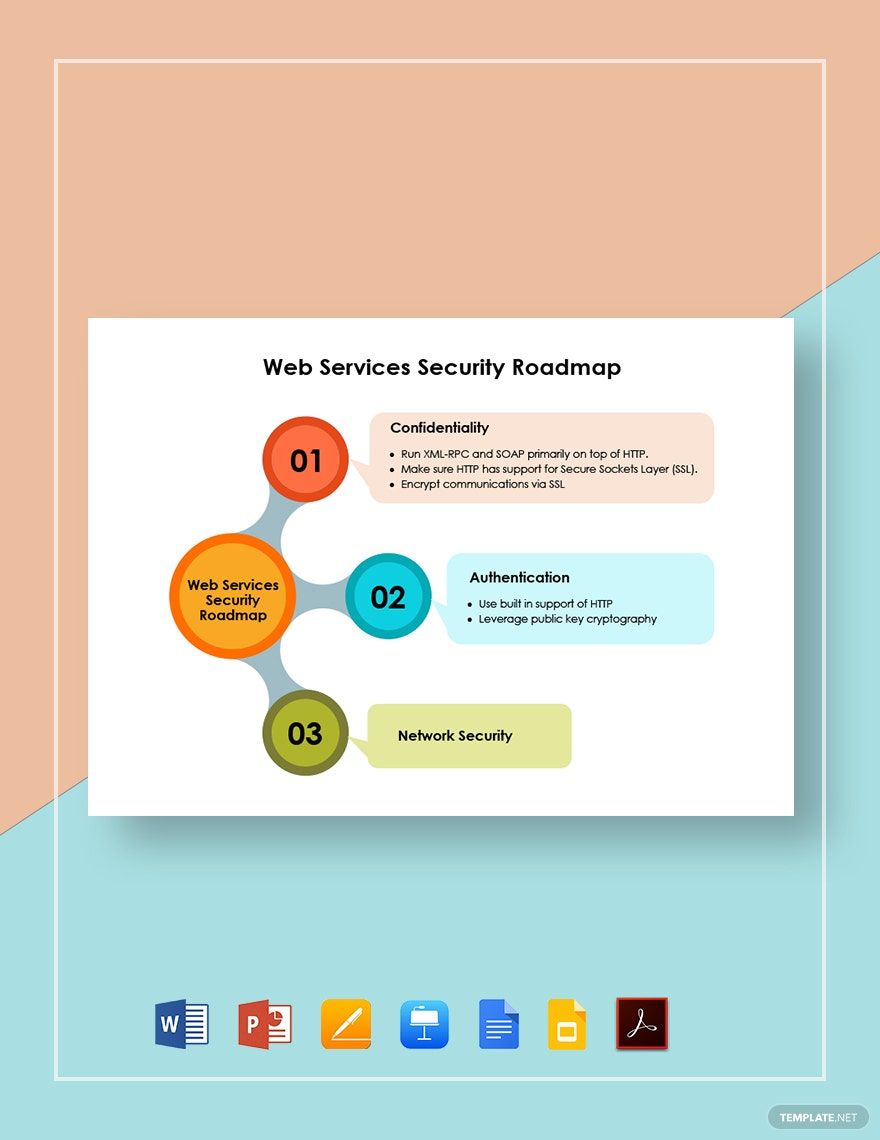
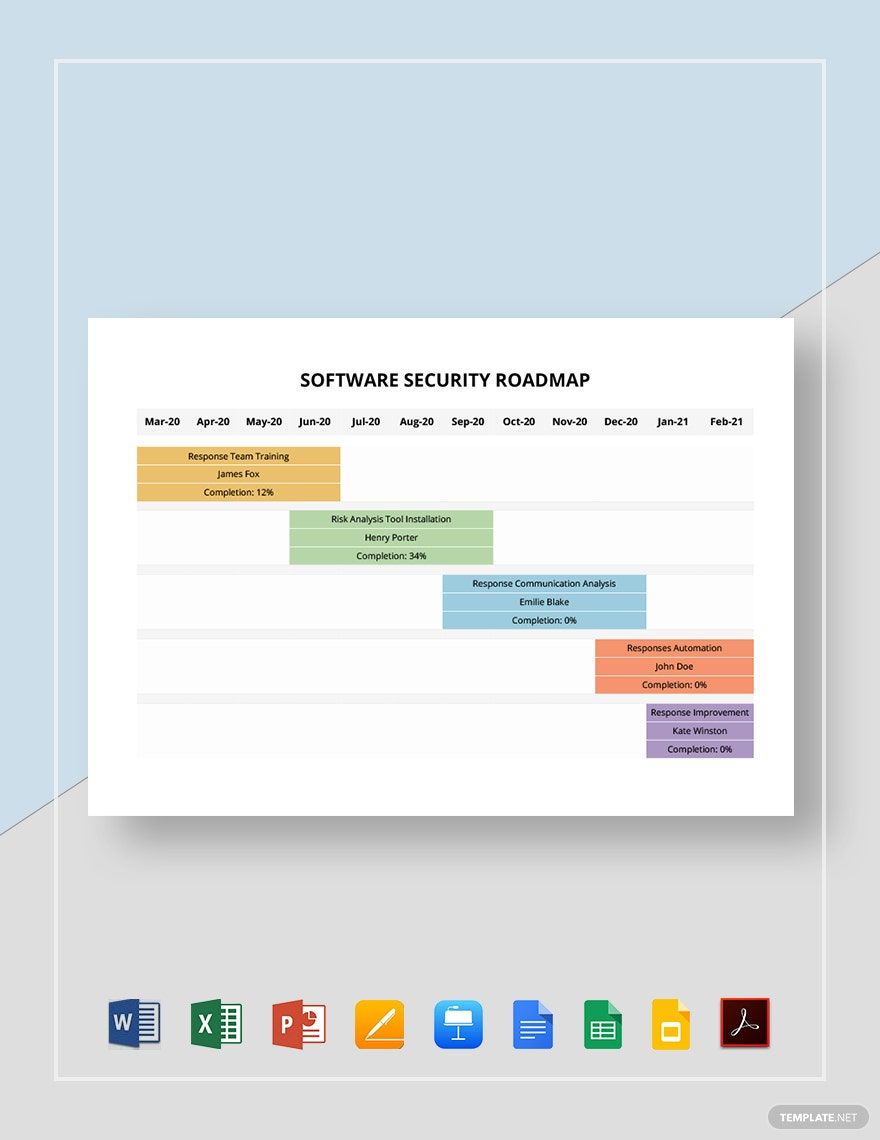
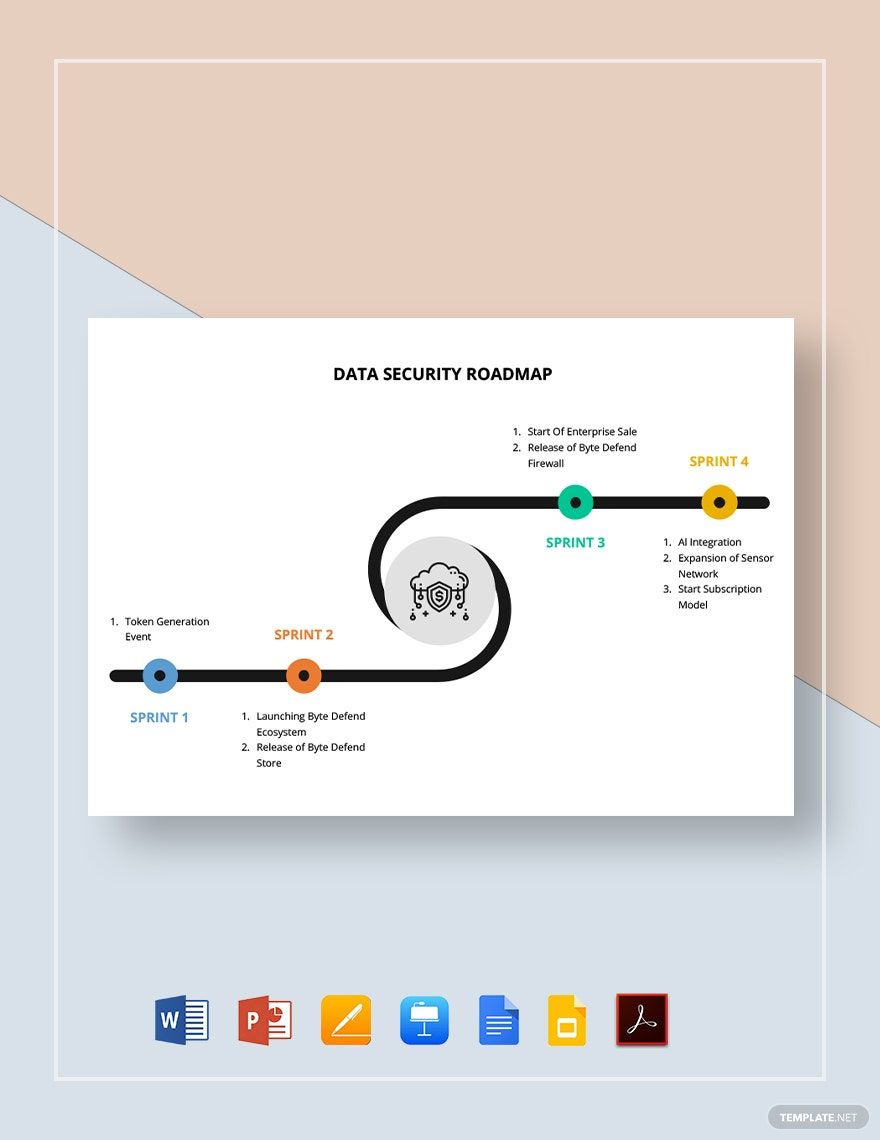
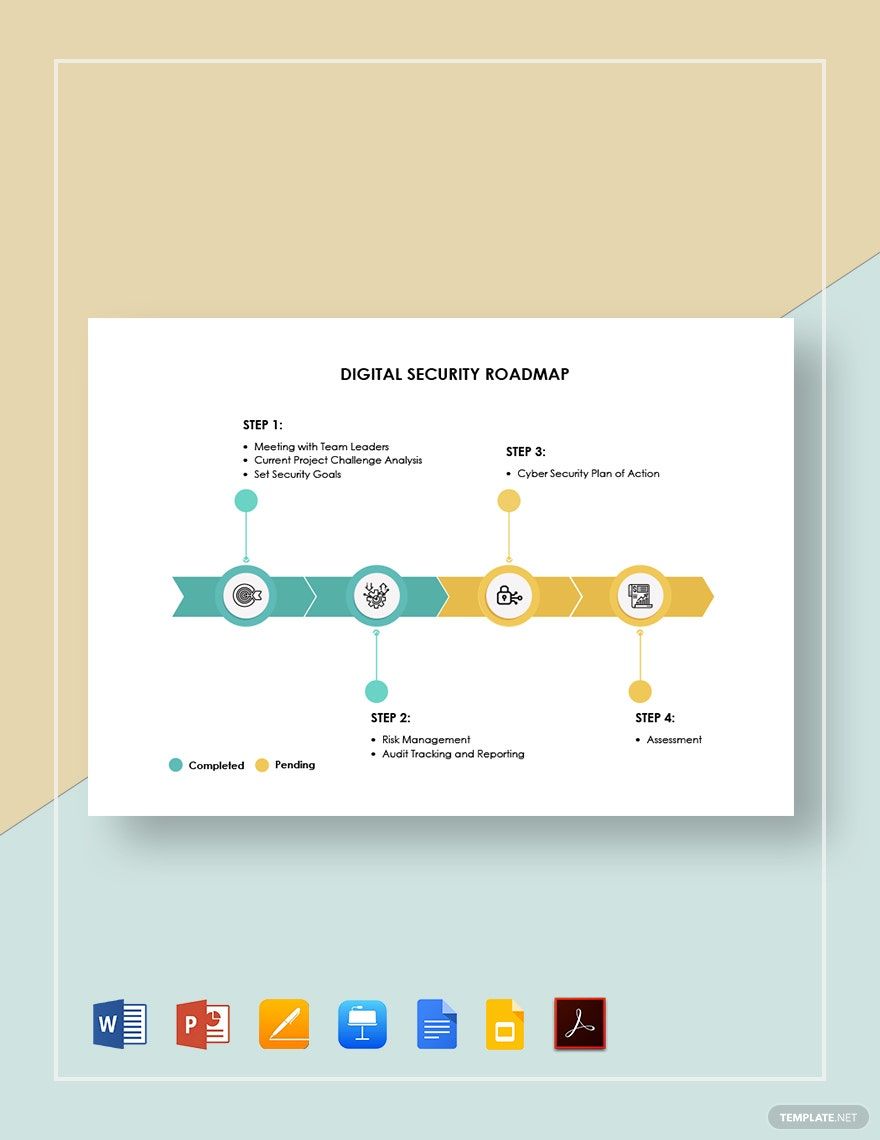
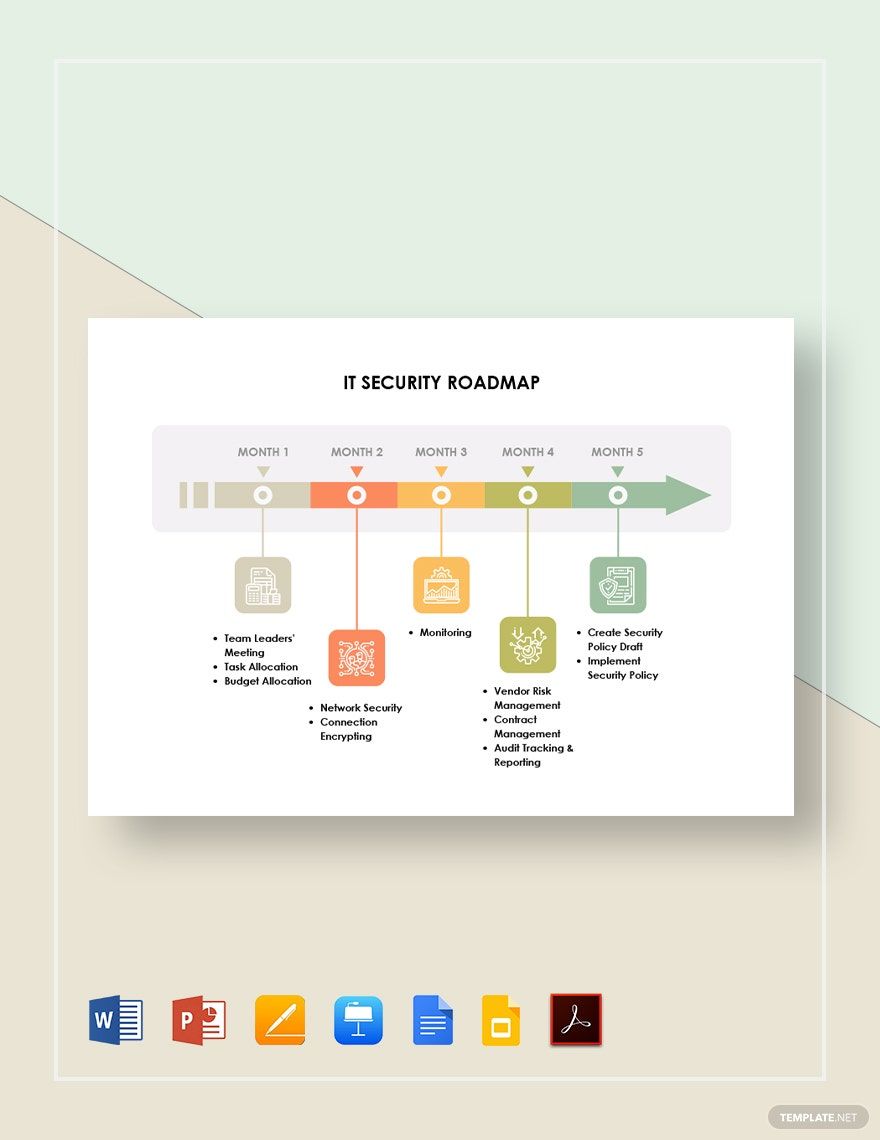
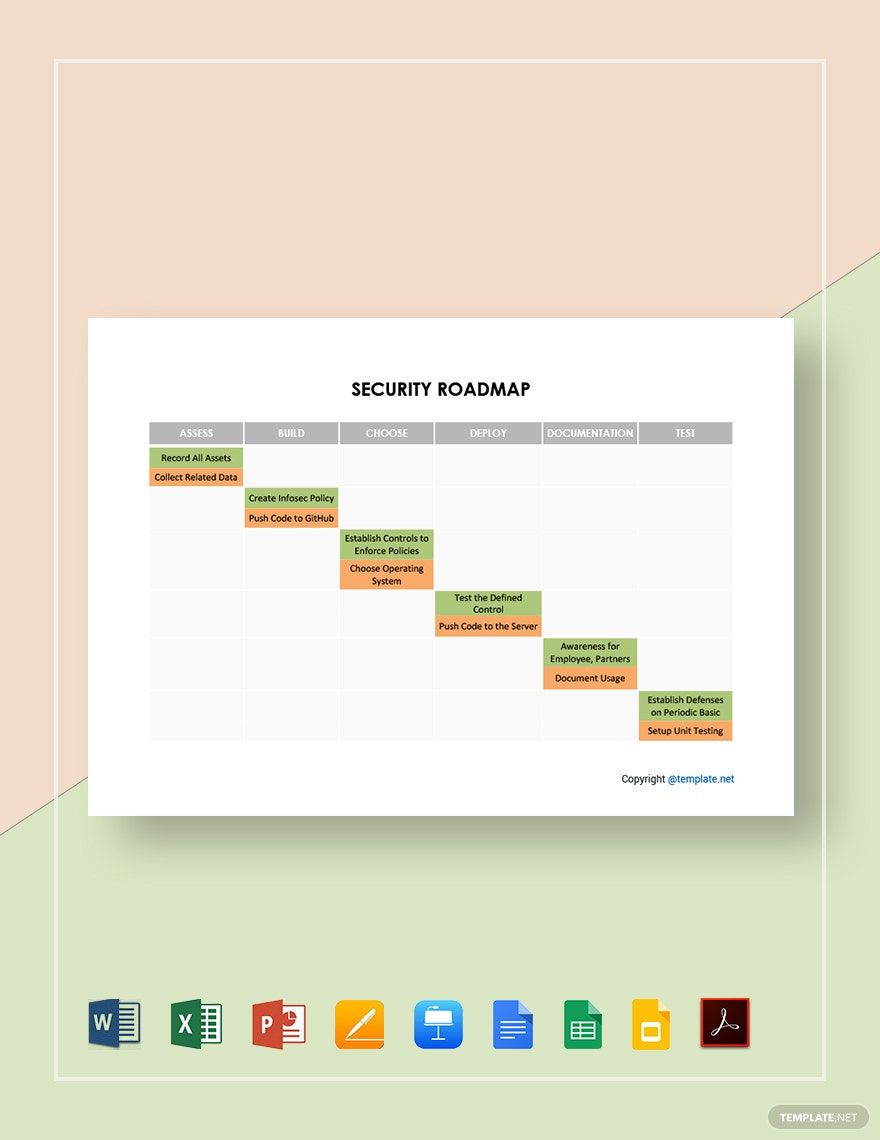
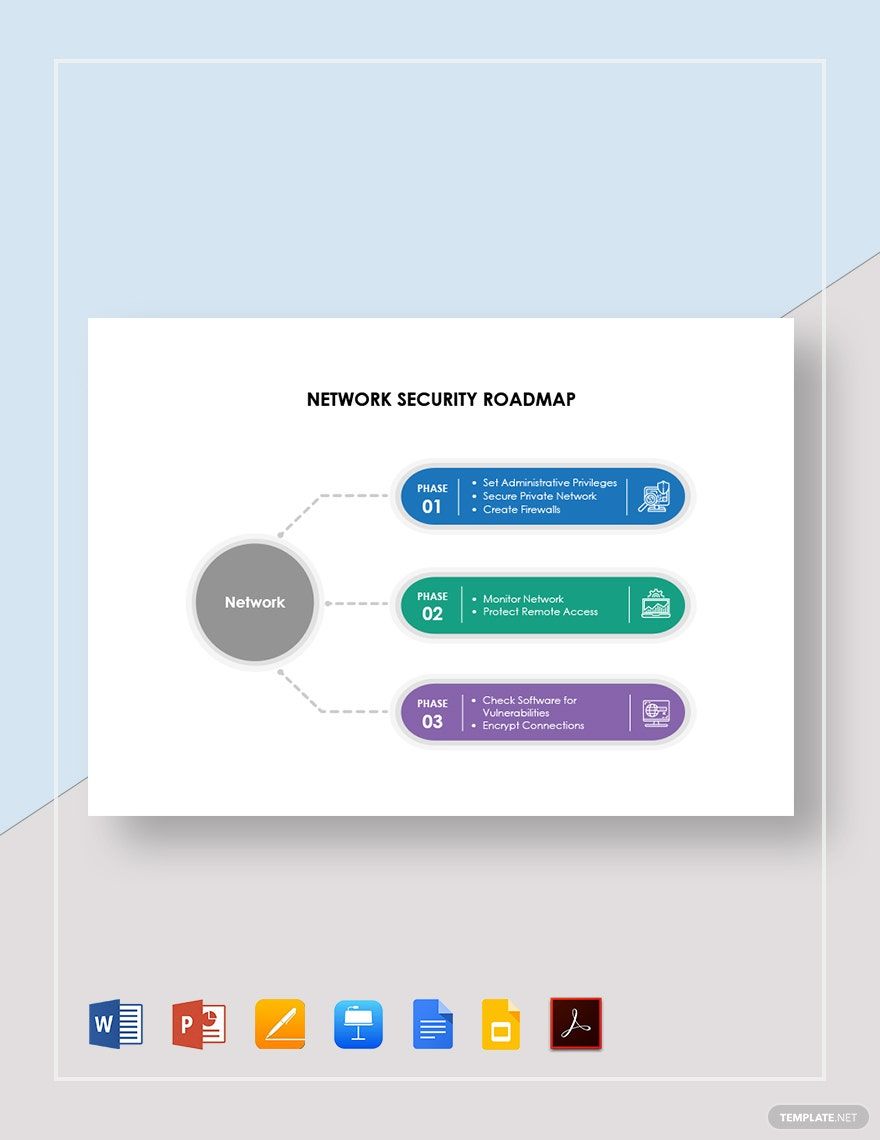
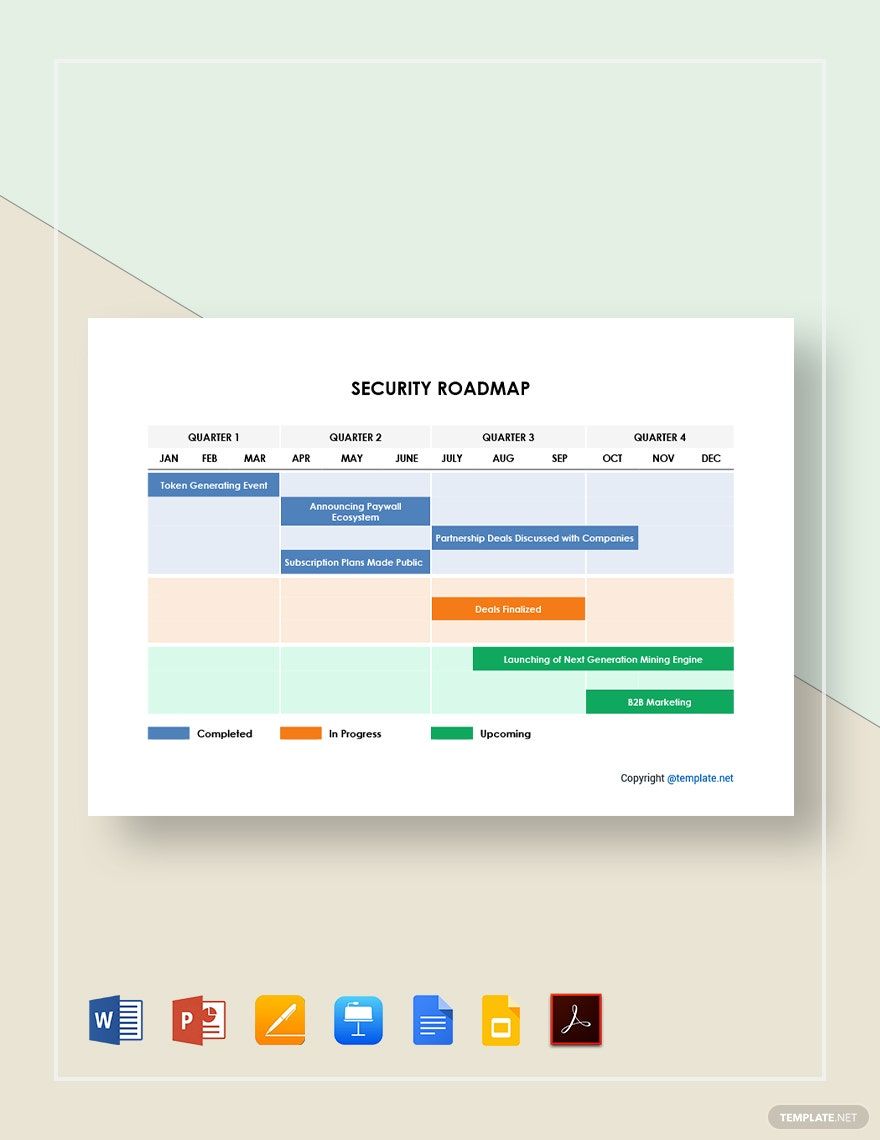
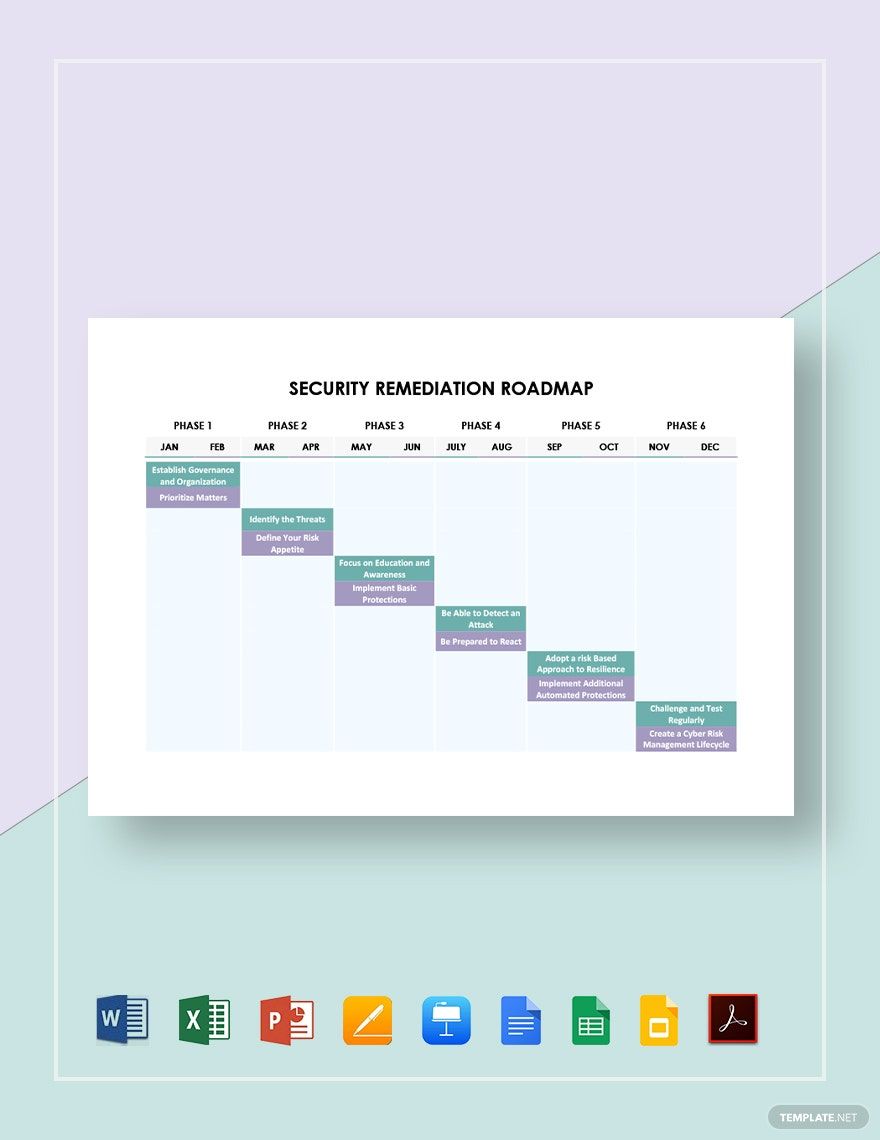
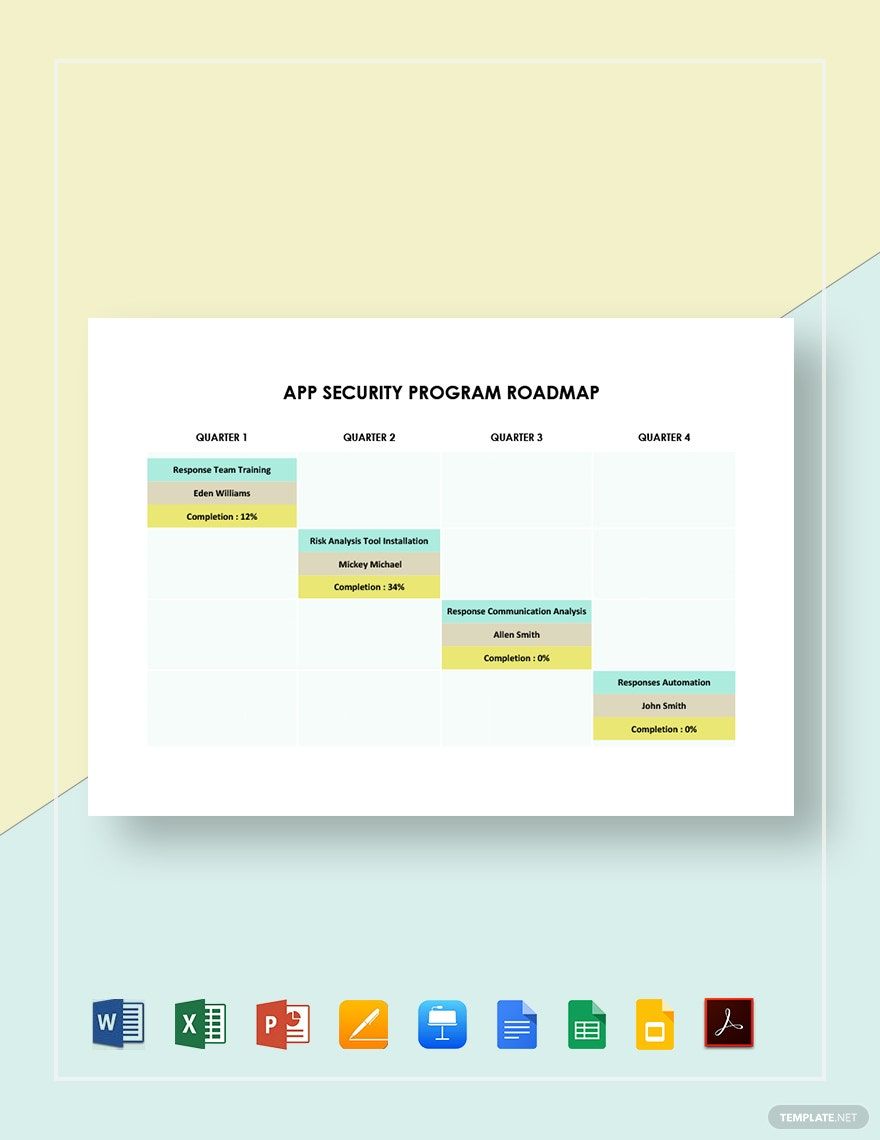
Keep your organization aligned, anticipate potential security threats, and ensure optimal protection with the Security Roadmap Templates from Template.net. These templates are designed for IT professionals, corporate security planners, and project managers who wish to accomplish efficient and thorough security planning. Use them to effectively map out a strategic security rollout for your next big product launch or to communicate updated security protocols company-wide. Each template includes key areas such as timeframes, roles, and responsibilities, all formatted for easy customization. No design skills are needed to personalize your roadmap, and you can achieve professional-grade results whether for a printed report or a digital presentation.
Discover the many Security Roadmap Templates we have on hand, which cater to varied yet specific needs. Start by selecting a template that fits your scope; then, easily swap in your assets, like company logos or proprietary data, and tweak the colors and fonts to align with your corporate branding. Advanced customization is straightforward—drag-and-drop icons or graphics, add animated effects for an engaging presentation, and even utilize AI-powered text tools to help articulate your plans concisely. These templates make creating detailed, attractive roadmaps fun and barrier-free, with endless possibilities at your fingertips. We offer regularly updated templates, so you always have access to fresh, innovative designs. When you're finished, conveniently download or share your roadmap via email, print, or direct link.